G Network Security Setup for Wireless Networks: A Comprehensive Guide
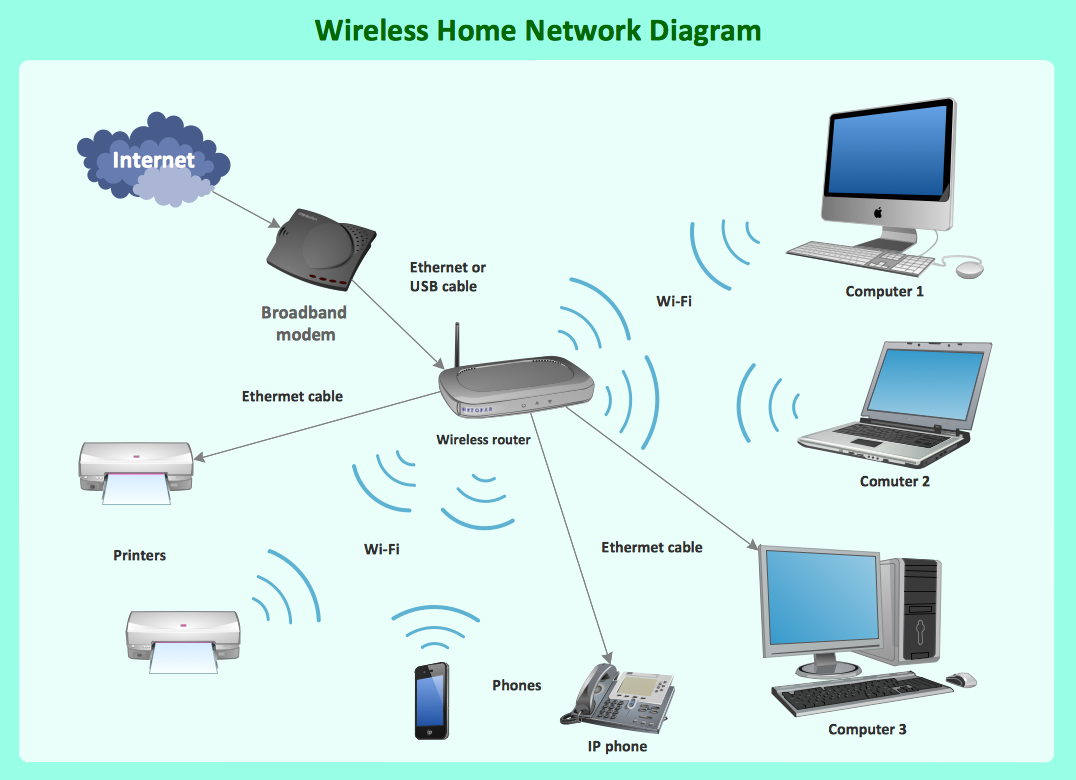
Wireless network security is crucial for protecting wireless networks and services from unwanted attacks. In today's digital age, securing your wireless network is essential to safeguard your data, devices, and online activities. A well-configured G network security setup for wireless networks can help prevent unauthorized access, theft, or damage to your network and devices.
Why Network Security Matters for Wireless Networks
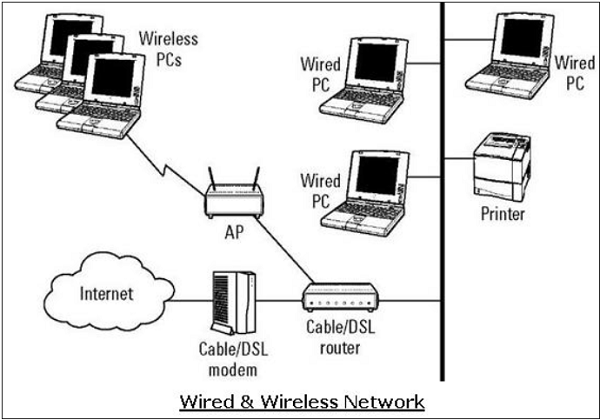
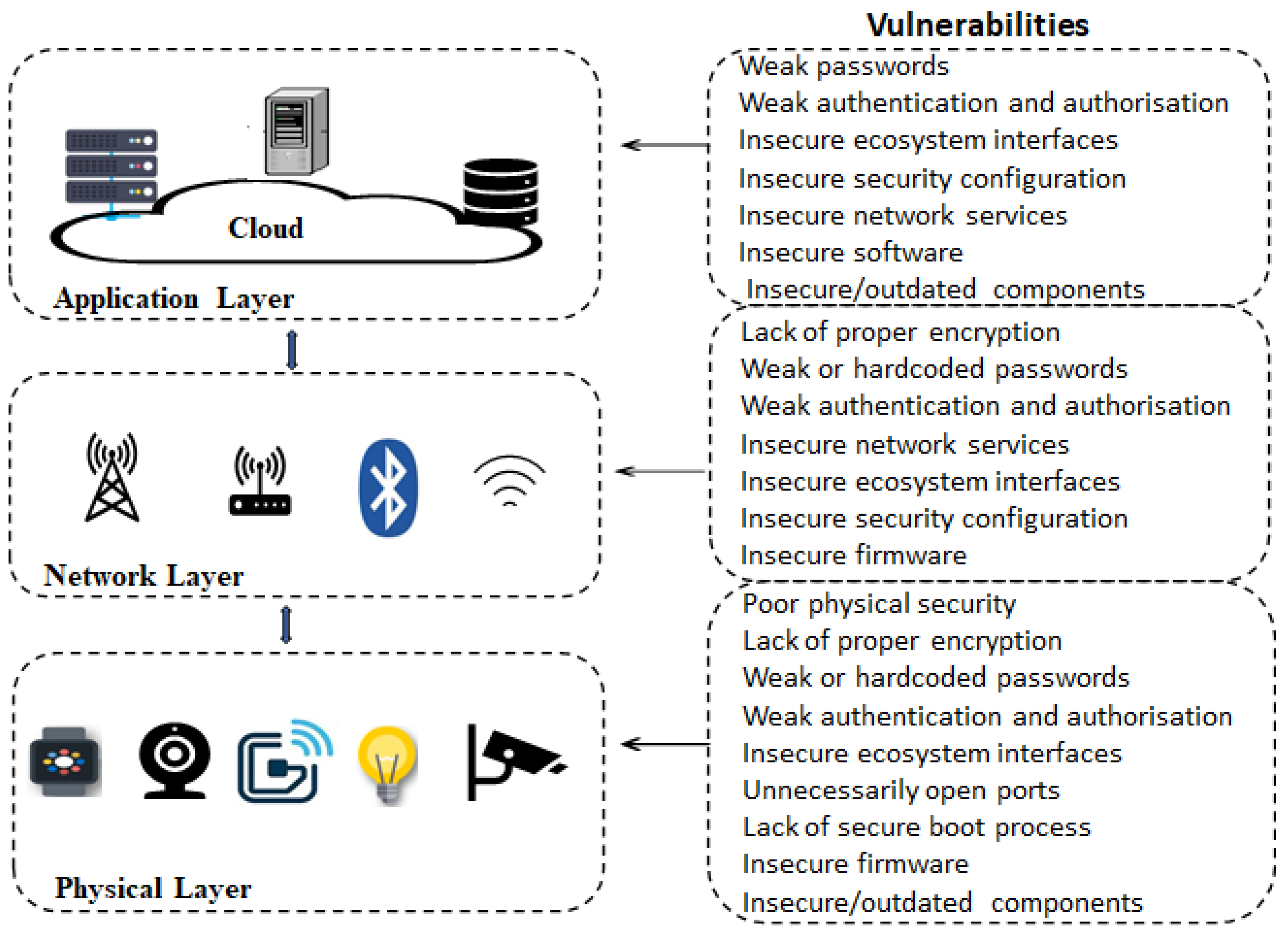
Wireless networks introduce additional security risks compared to wired networks. Unsecured wireless networks can be vulnerable to hacking, eavesdropping, and other cyber threats. This is because wireless signals can be intercepted by malicious actors, who can then gain access to your network and devices. A G network security setup for wireless networks can help mitigate these risks and ensure the security of your online activities.

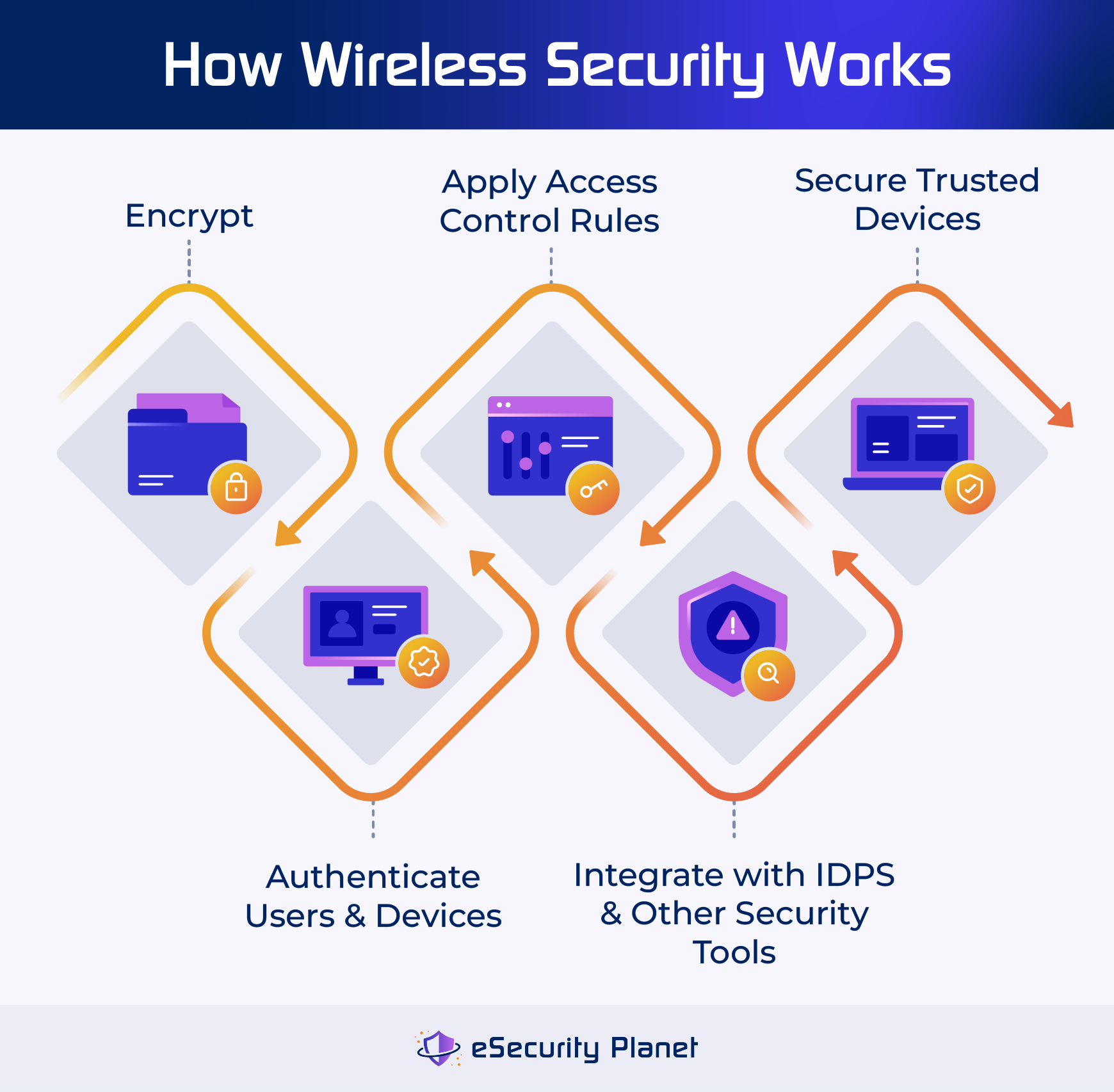
G Network Security Setup for Wireless Networks: Best Practices
To setup a secure G network for wireless networks, follow these best practices:
- Use WPA3 Protocol:** WPA3 is the latest generation of Wi-Fi security protocol, offering advanced security features to protect your network and devices. It's essential to use WPA3 protocol to ensure the security of your wireless network.
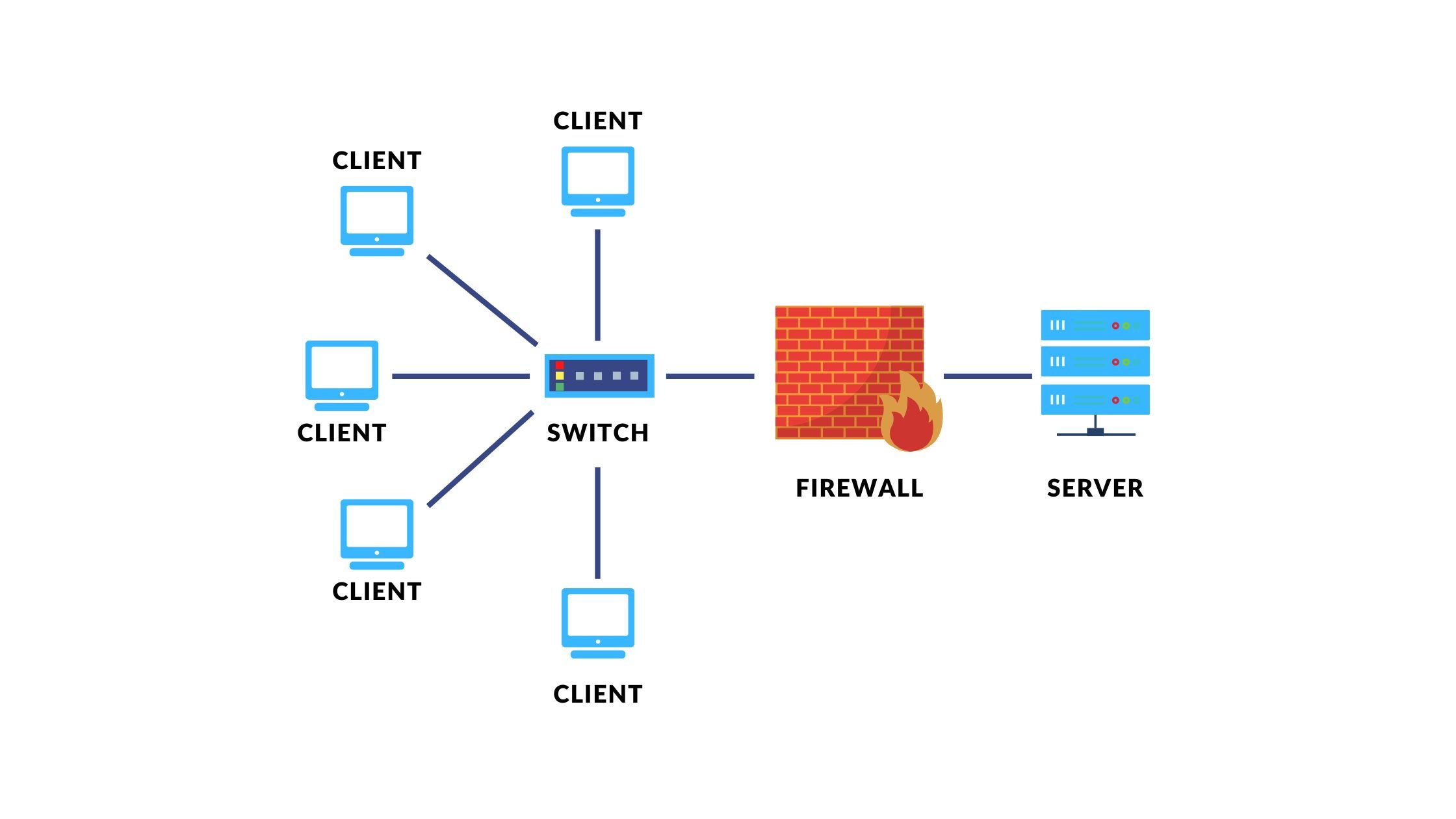
- Configure Encryption:** Enable encryption on your wireless network to prevent unauthorized access. Use WPA2 encryption or WPA3 encryption, depending on your network configuration.
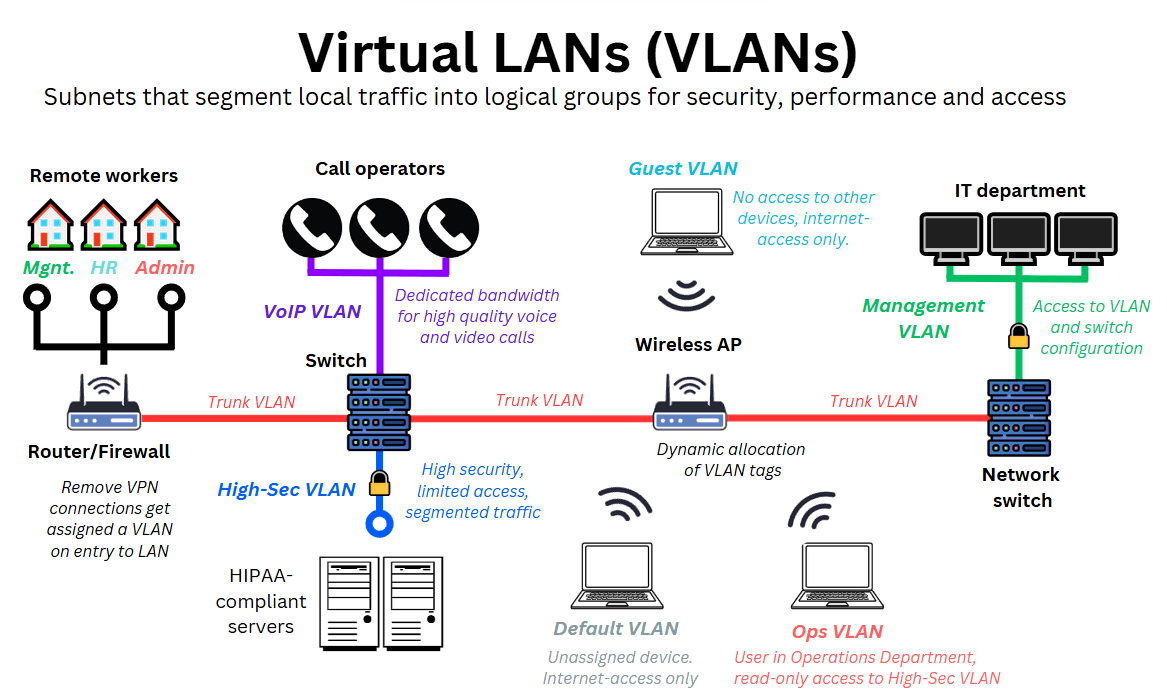
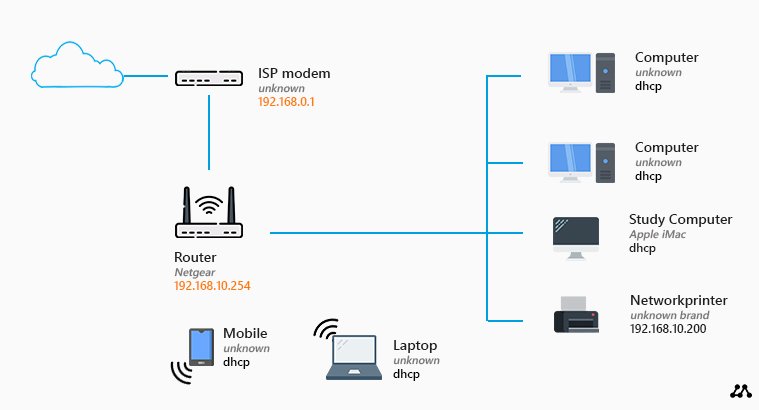
- Set Up Guest Network:** Create a separate guest network for visitors and contractors. This will prevent them from accessing your main network and devices.
- Use Strong Passwords:** Use strong, unique passwords for your network and devices. Avoid using default passwords or easily guessable passwords.
- Regularly Update Firmware:** Regularly update your router's firmware to ensure you have the latest security patches and features.
- Monitor Your Network:** Regularly monitor your network for suspicious activity, and take action promptly if you detect any anomalies.
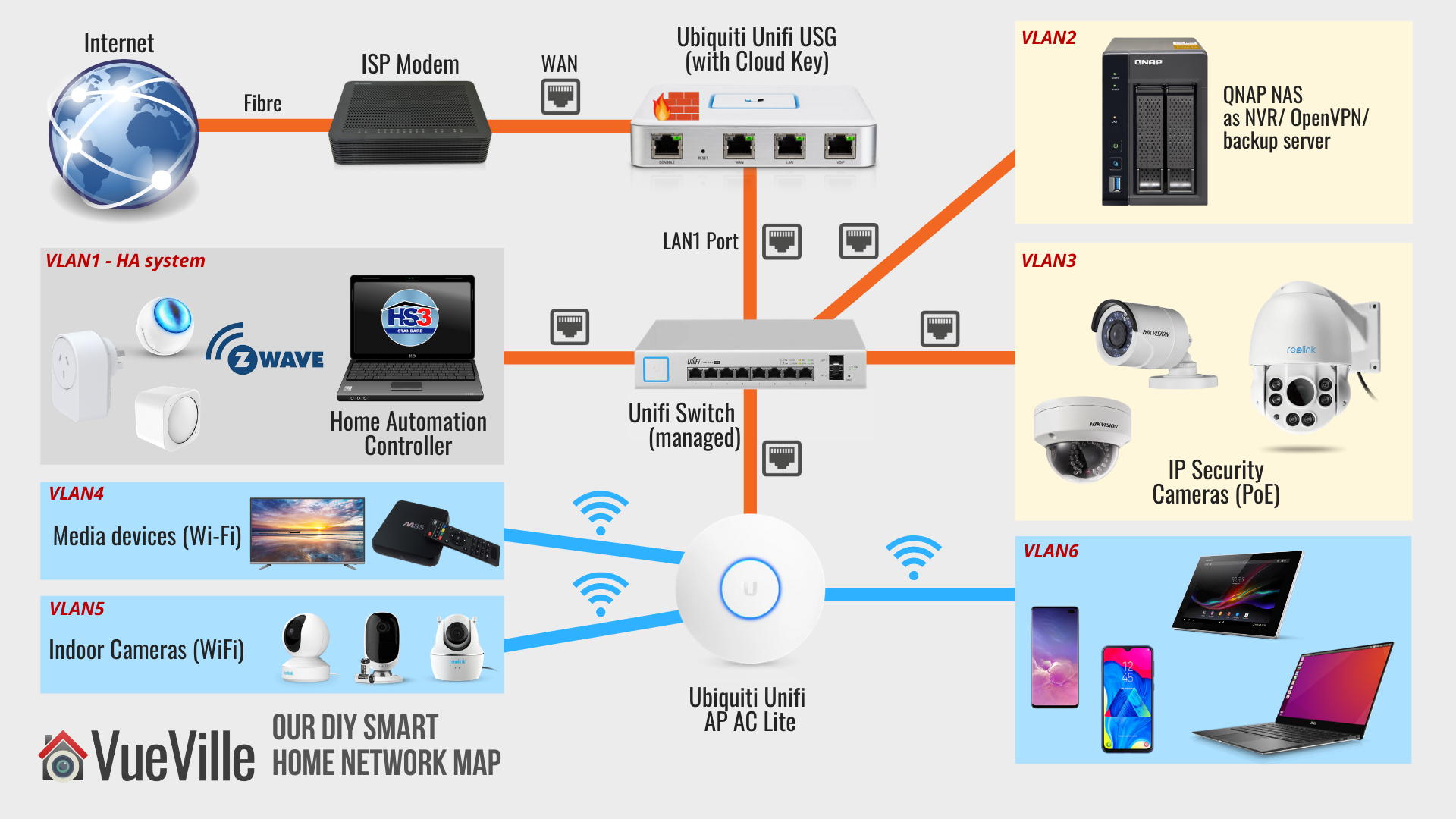
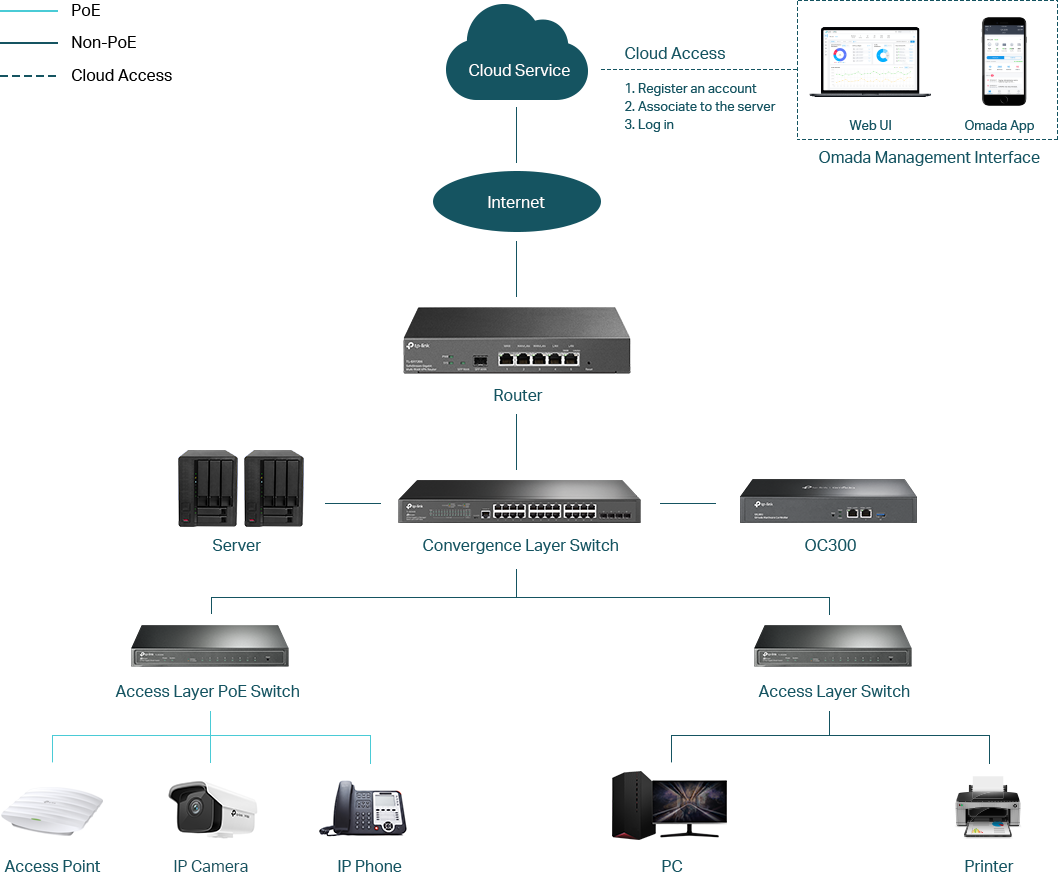
- Use Network Segmentation:** Segment your network into different VLANs (Virtual Local Area Networks) to prevent lateral movement in case of a security breach.
- Implement Intrusion Detection and Prevention:** Use intrusion detection and prevention systems to monitor your network for potential security threats.