G Network Setup for Secure Communication Protocols
In today's interconnected world, ensuring the security of communication protocols is crucial for protecting sensitive data and maintaining the integrity of online transactions. With the rise of cyber threats and vulnerabilities, it's essential to understand the importance of network security protocols like TLS, IPsec, and SSH in safeguarding our online activities. In this article, we'll delve into the world of G Network Setup for Secure Communication Protocols, exploring the nuances of these protocols and how they can be used to protect our online communications.
Basics of Network Security Protocols
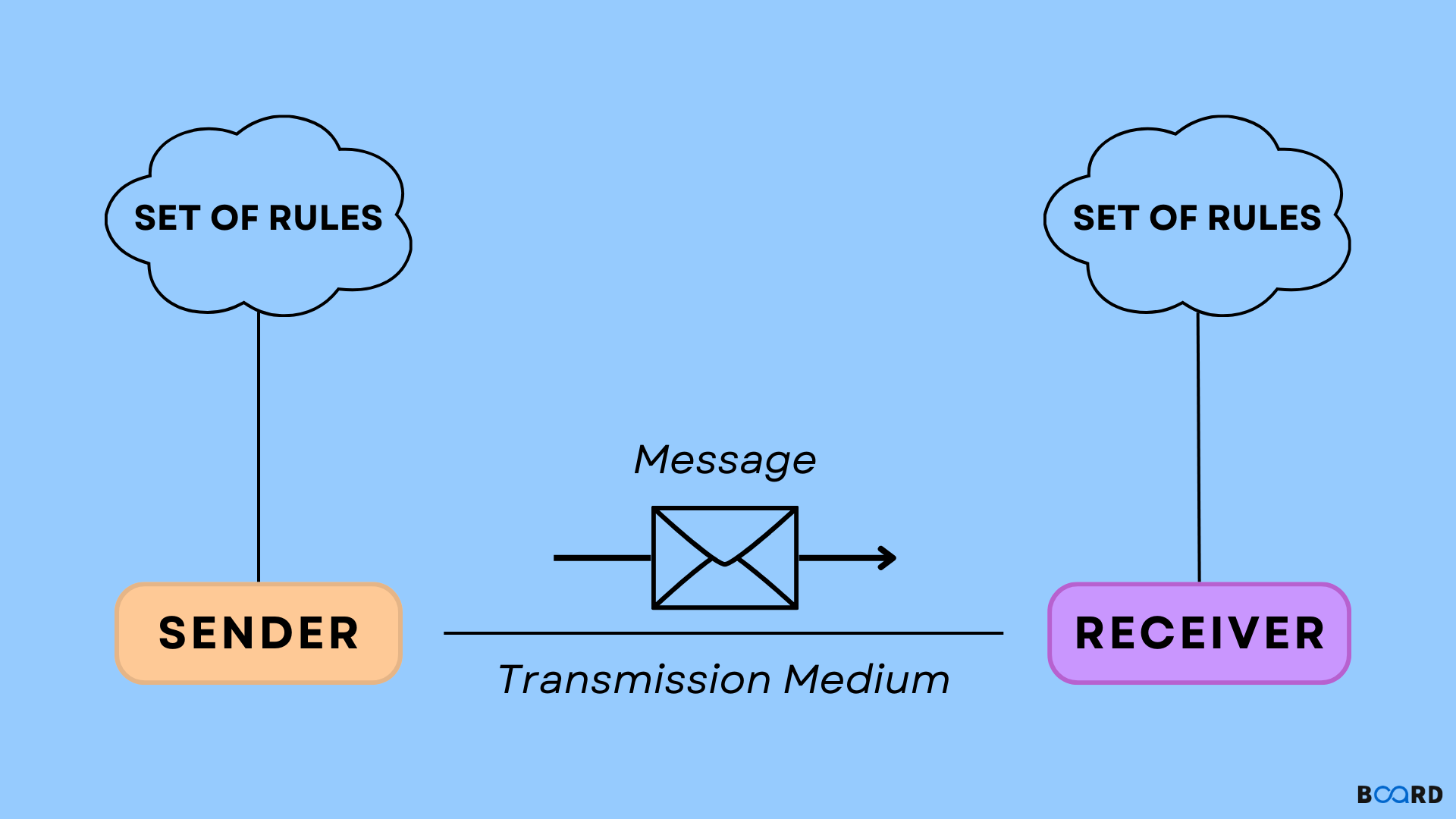
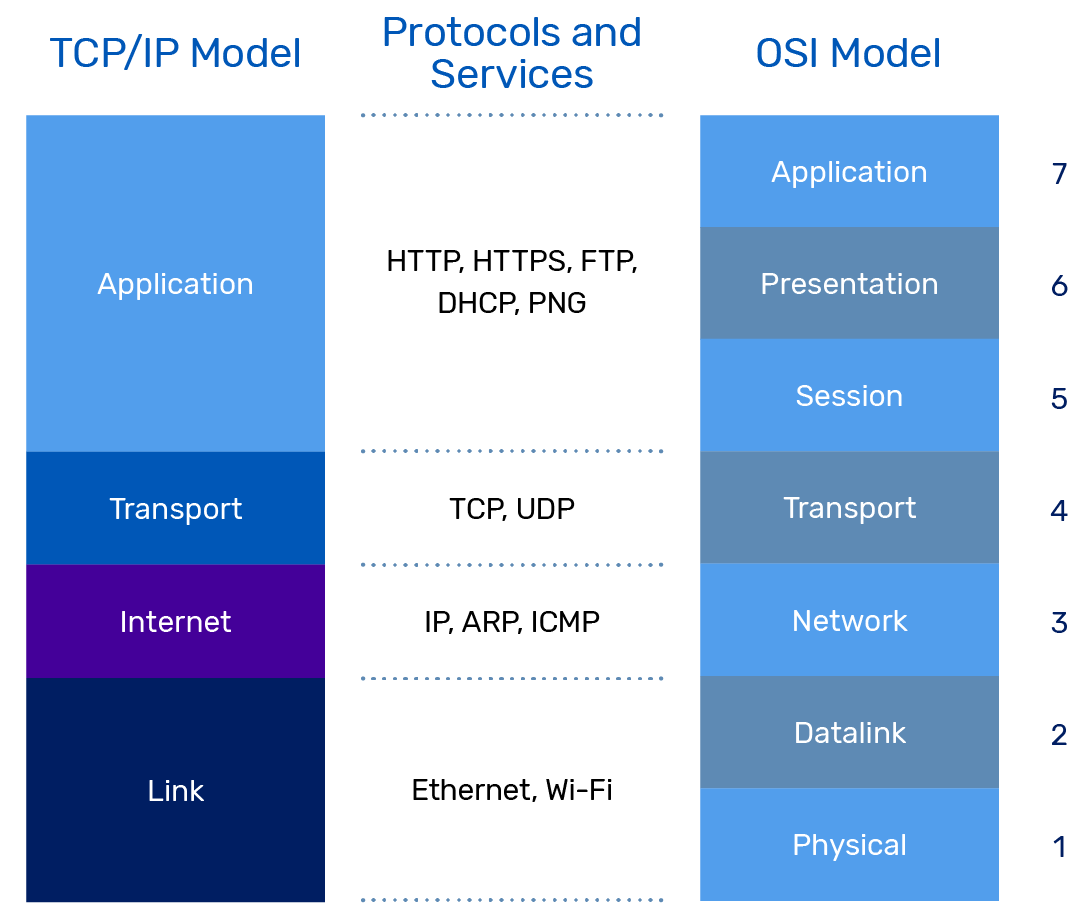
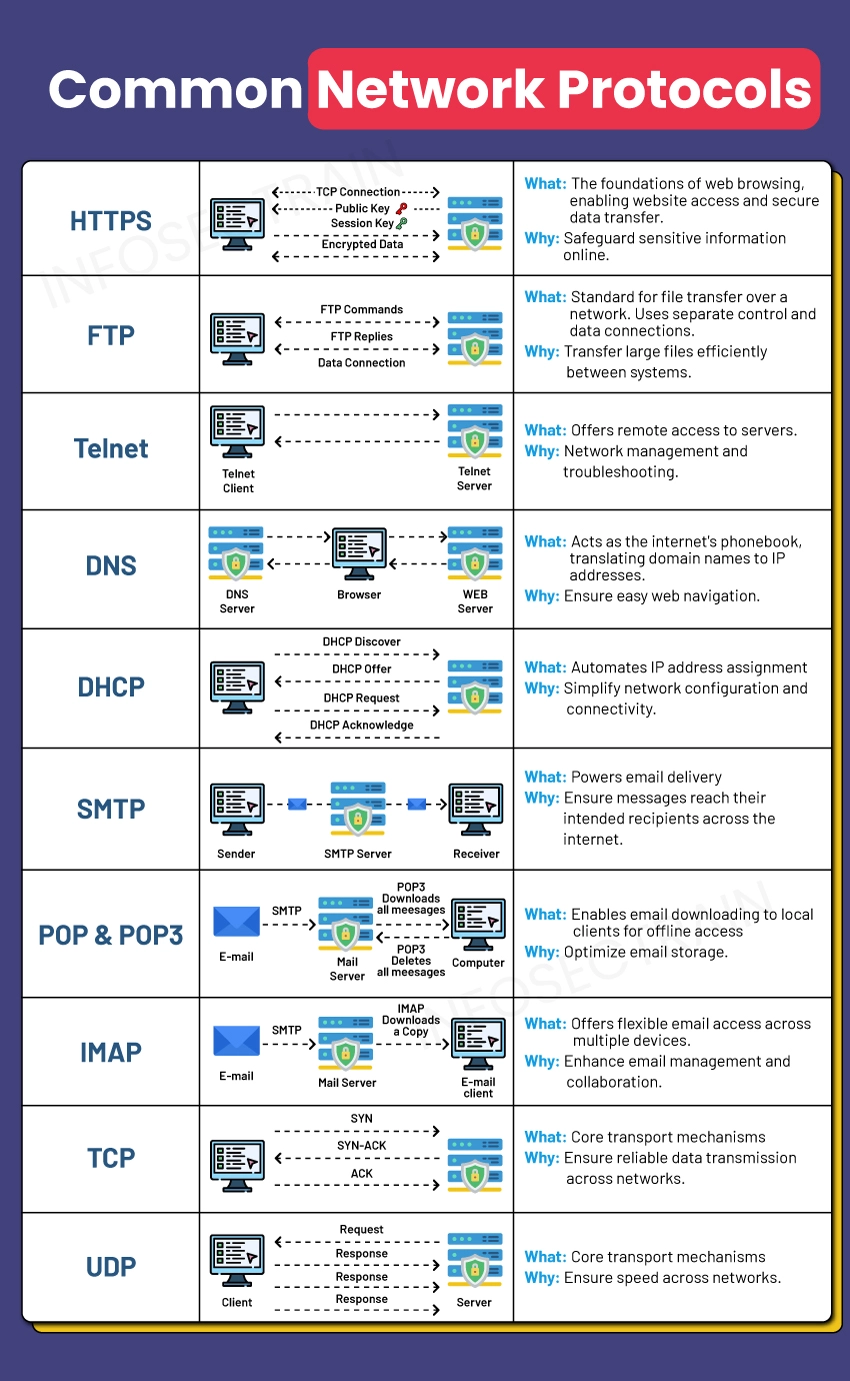
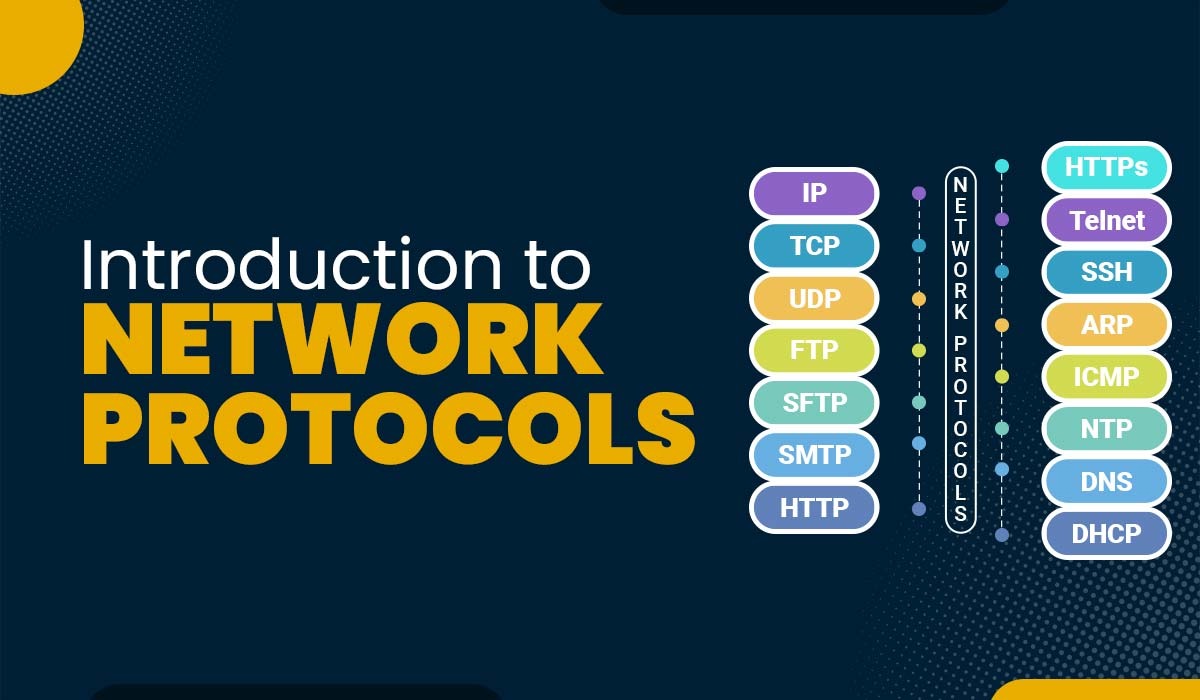
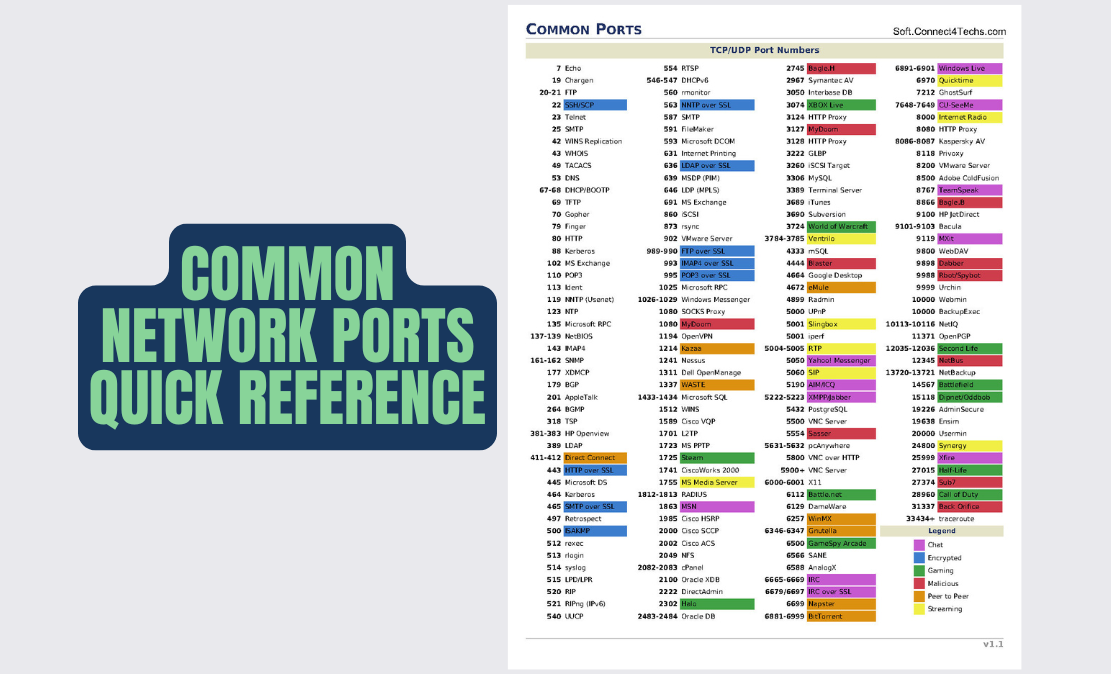
Network security protocols are designed to protect the confidentiality, integrity, and availability of Internet communications between network hosts, gateways, and devices. At the heart of these protocols lie the cryptographic algorithms that ensure the secure transmission of data. Some of the most common network protocols include:
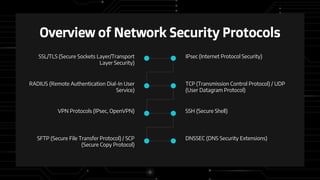
- Internet Protocol Security (IPsec)
- Secure Sockets Layer (SSL)
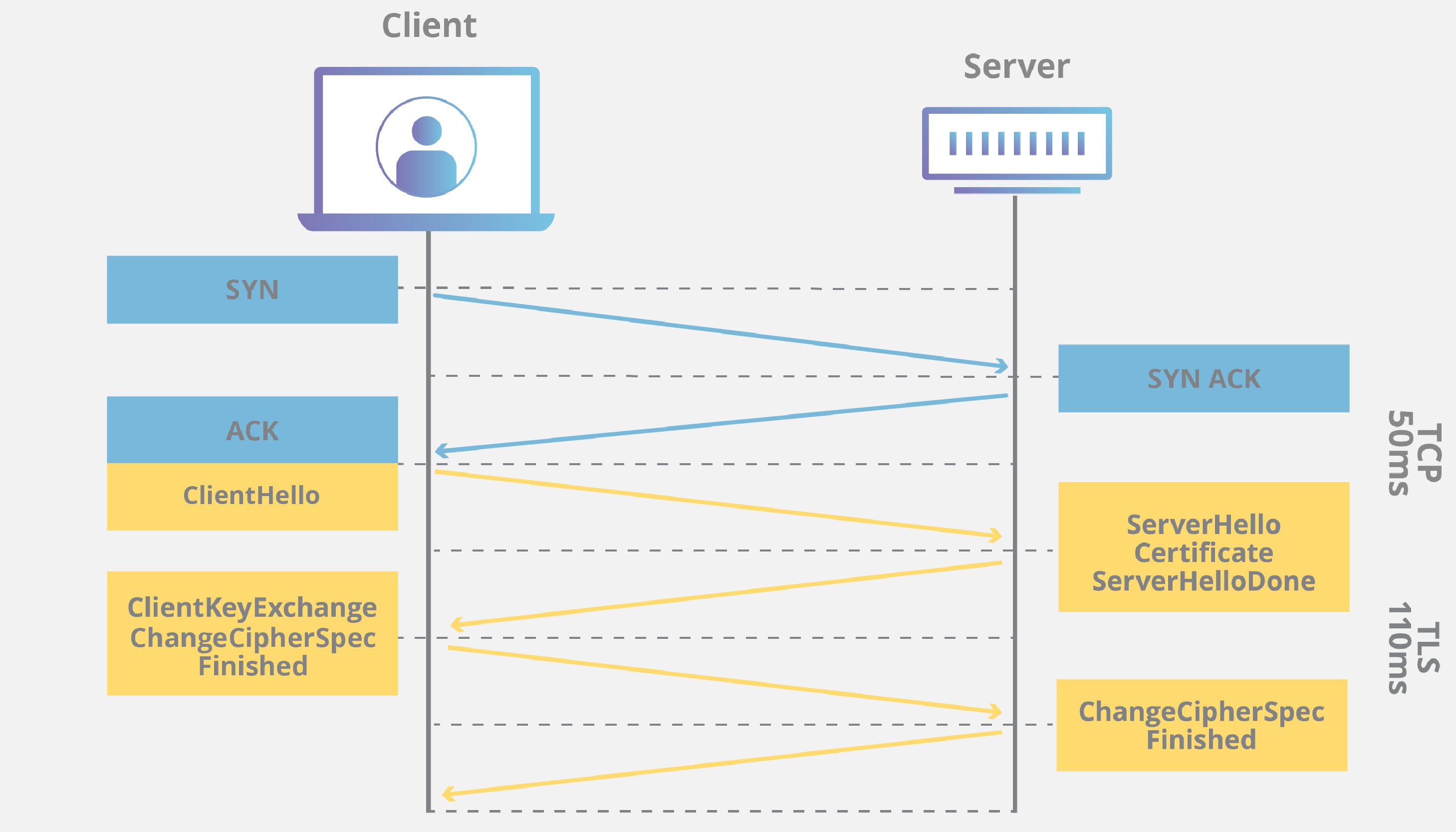
- Transport Layer Security (TLS)
- SSH
- IPSec
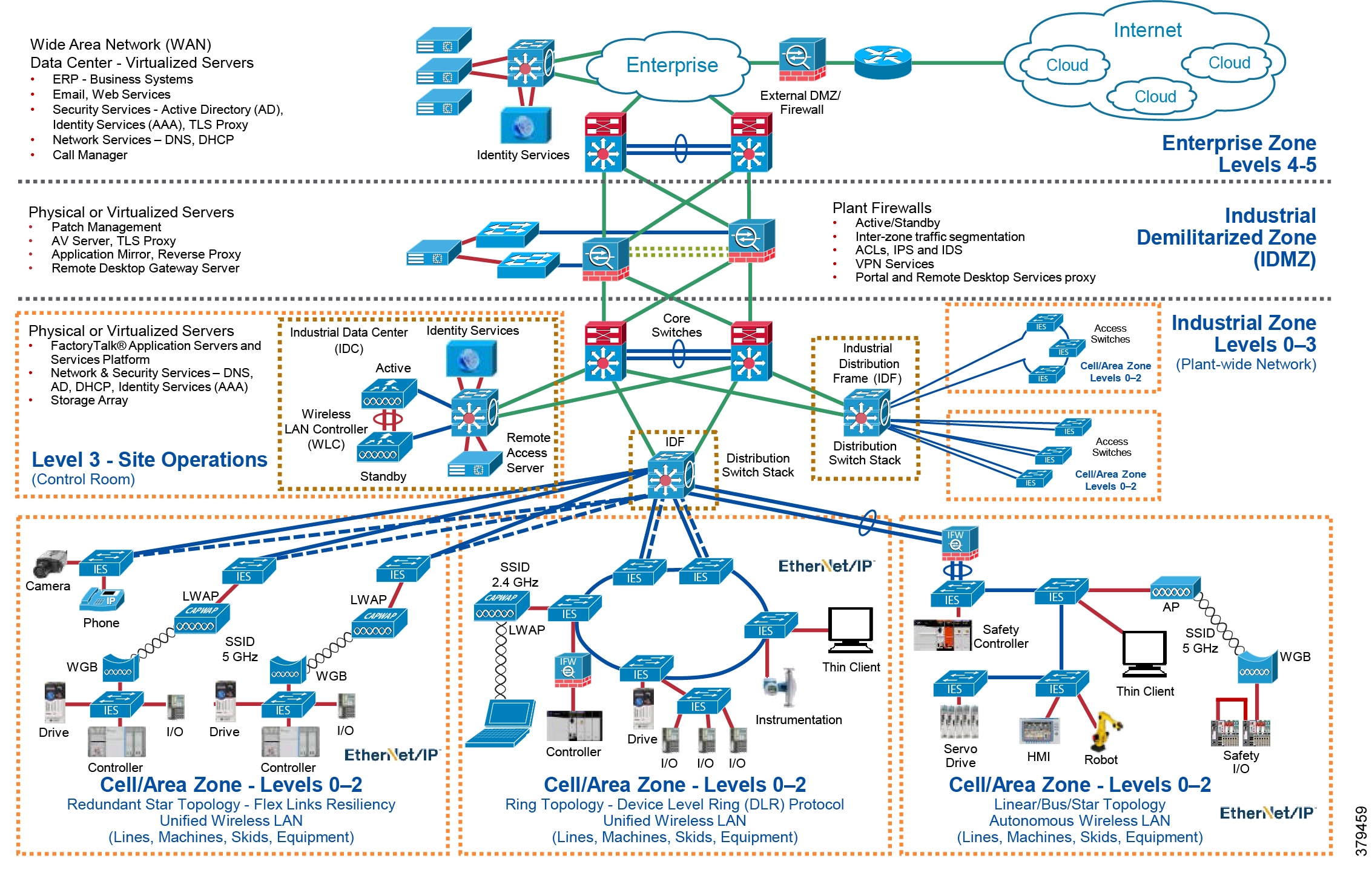
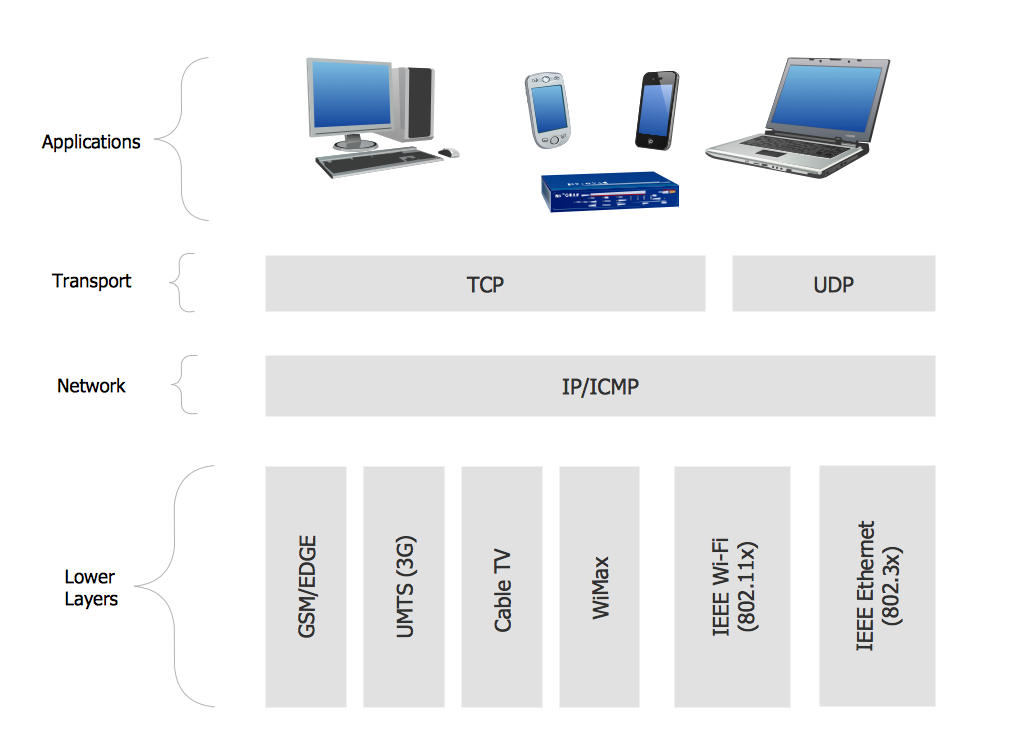
Understanding G Network Setup for Secure Communication Protocols
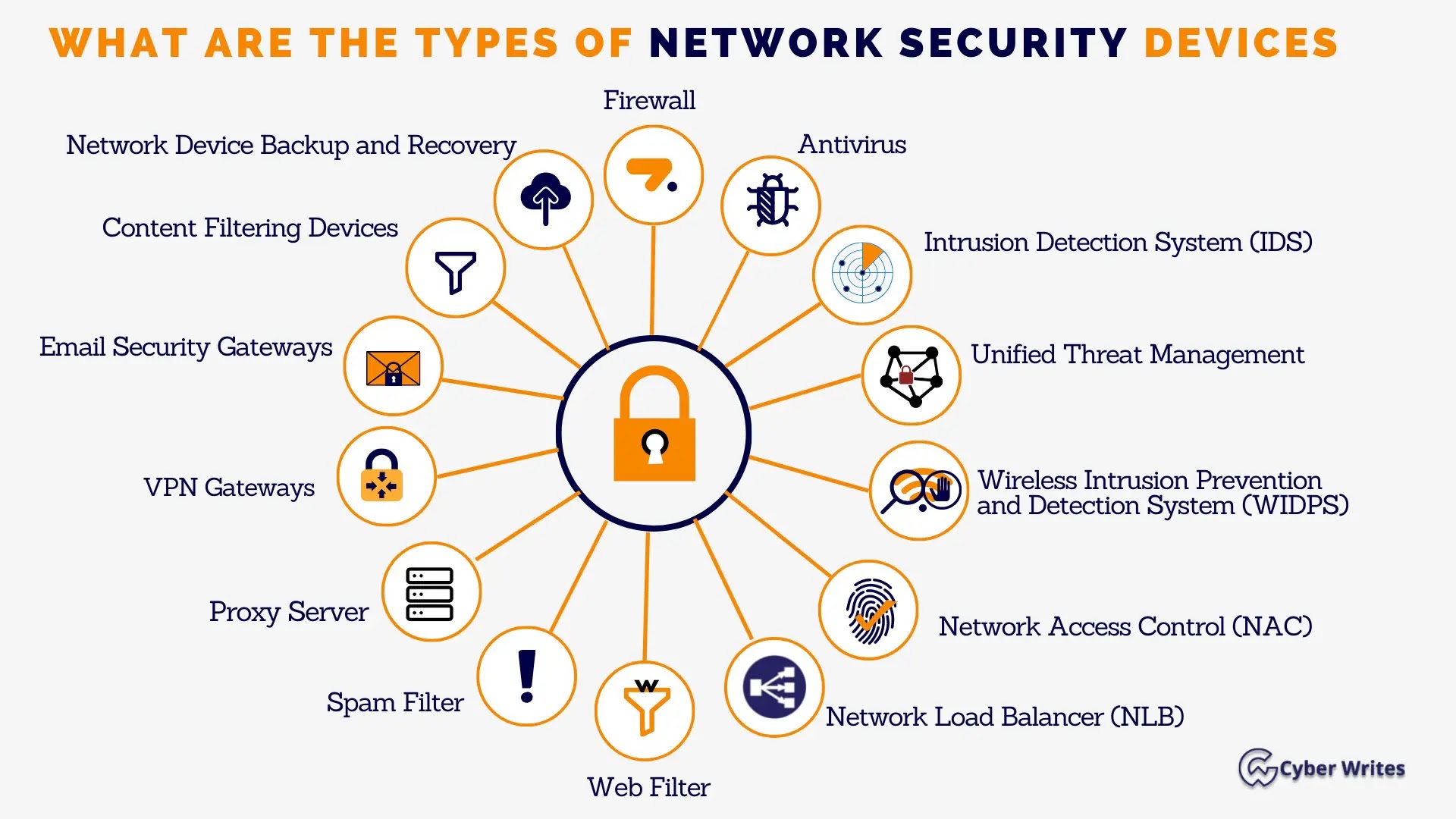
A G Network Setup for Secure Communication Protocols involves configuring network devices and infrastructure to ensure the secure transmission of data. This includes setting up nodes, routing protocols, and removing vulnerabilities. To achieve a secure network setup, it's essential to:








![Network Security Protocols [An Easy-to-Read Guide] - GoGet Secure Network Security Protocols [An Easy-to-Read Guide] - GoGet Secure](https://i.etsystatic.com/33185255/r/il/095720/6250887009/il_794xN.6250887009_og6q.jpg)




.png)