Understanding G Network Security Protocols: A Comprehensive Guide
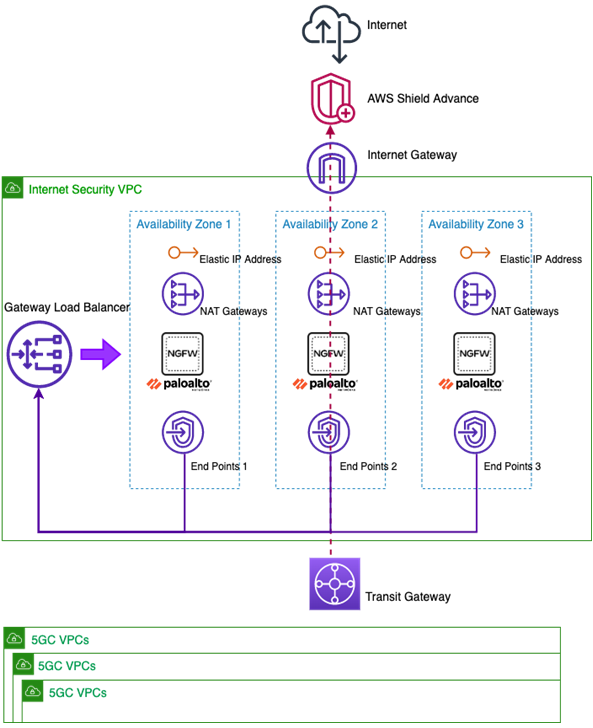
In today's digital age, network security is more crucial than ever. With the rise of cyber threats and data breaches, ensuring the integrity and security of data transmitted across network connections is essential. G Network Security Protocols are network protocols that ensure the confidentiality and integrity of data transmitted across network connections. In this article, we will explore the world of G Network Security Protocols and provide a comprehensive guide to understanding them.
What are G Network Security Protocols?
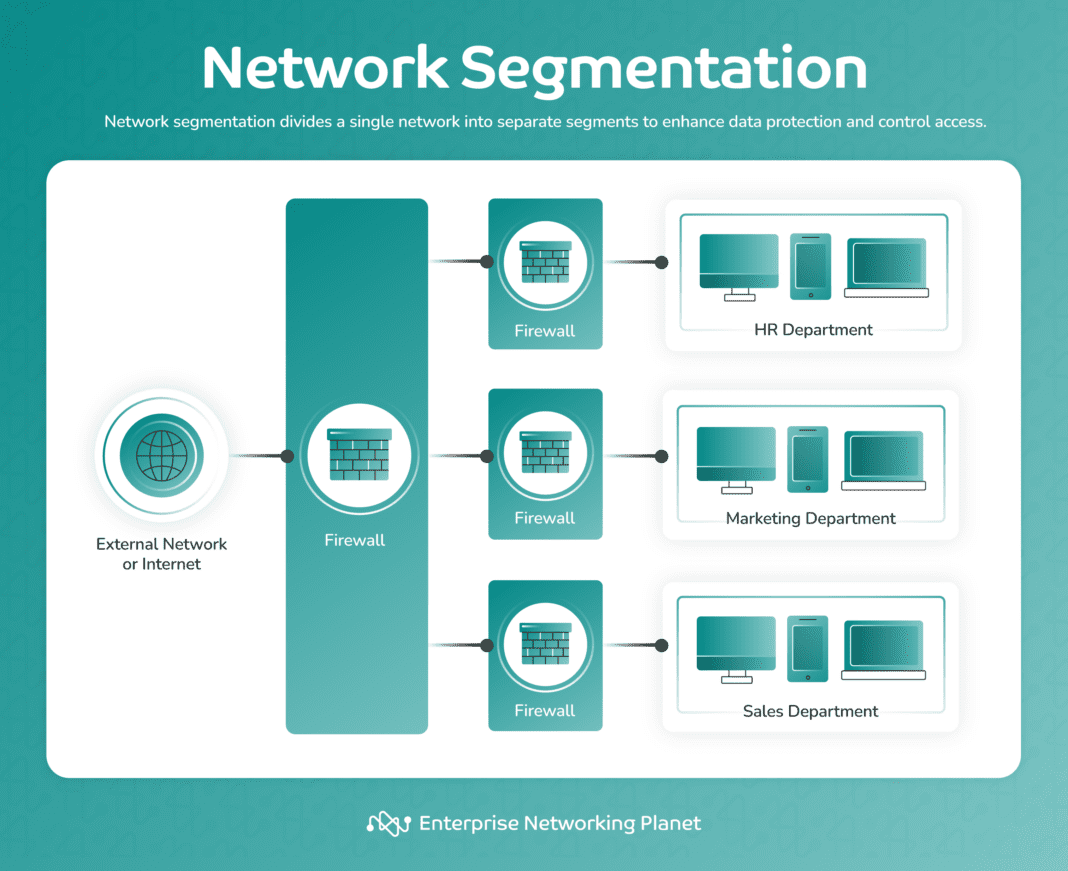
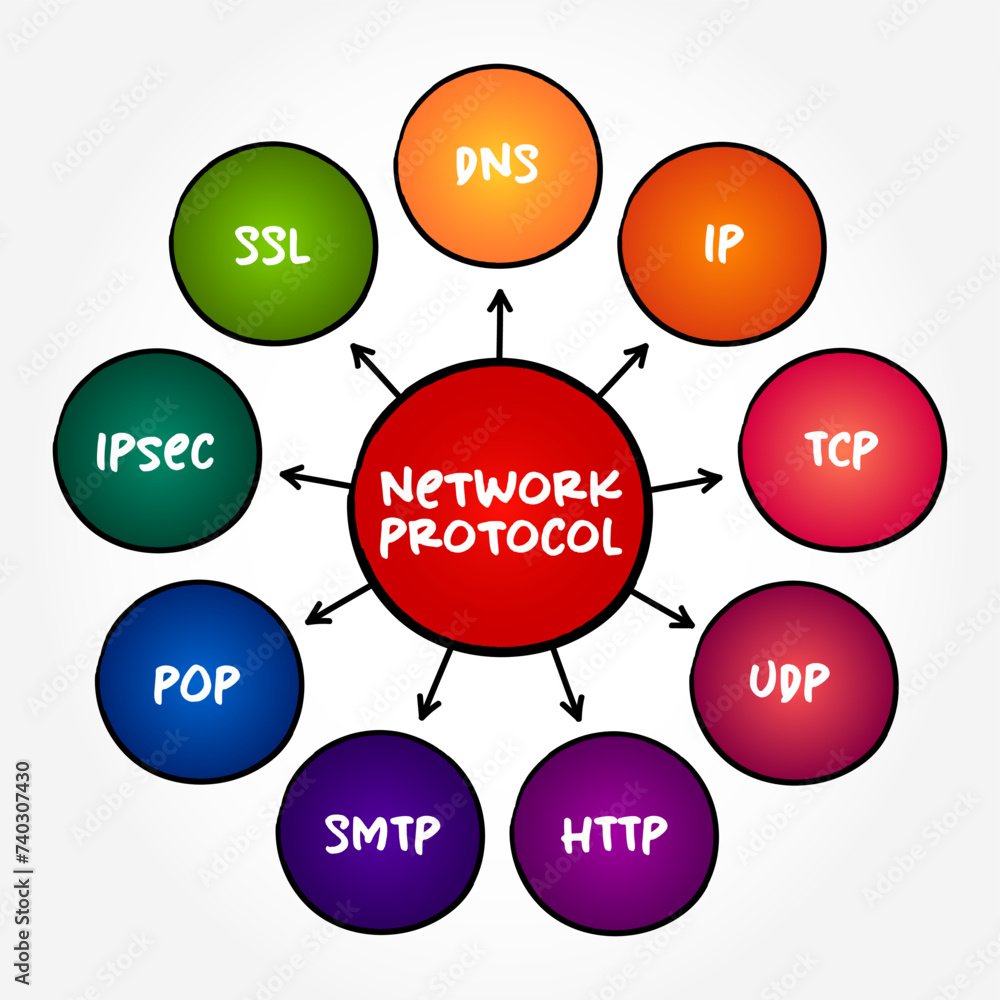
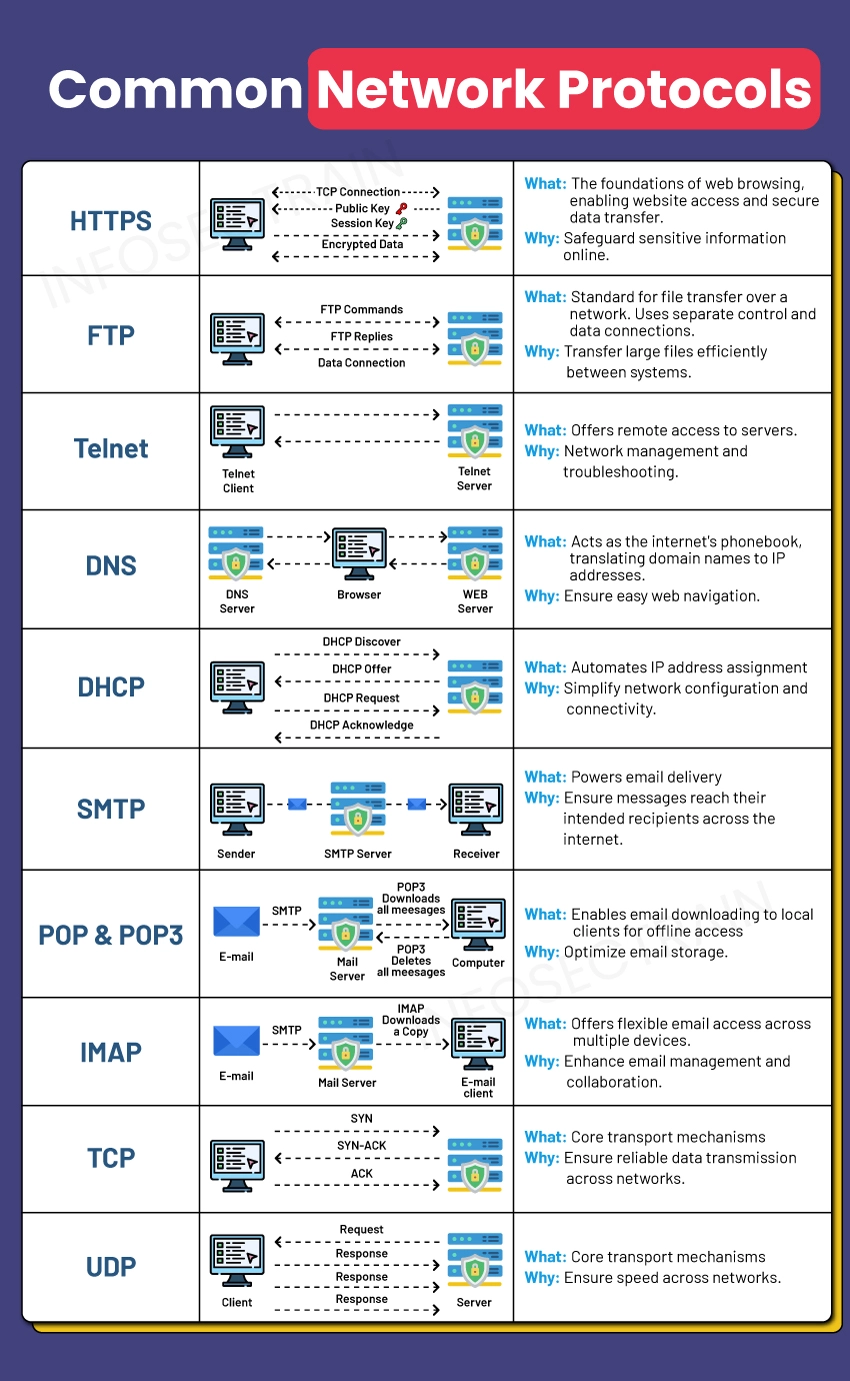
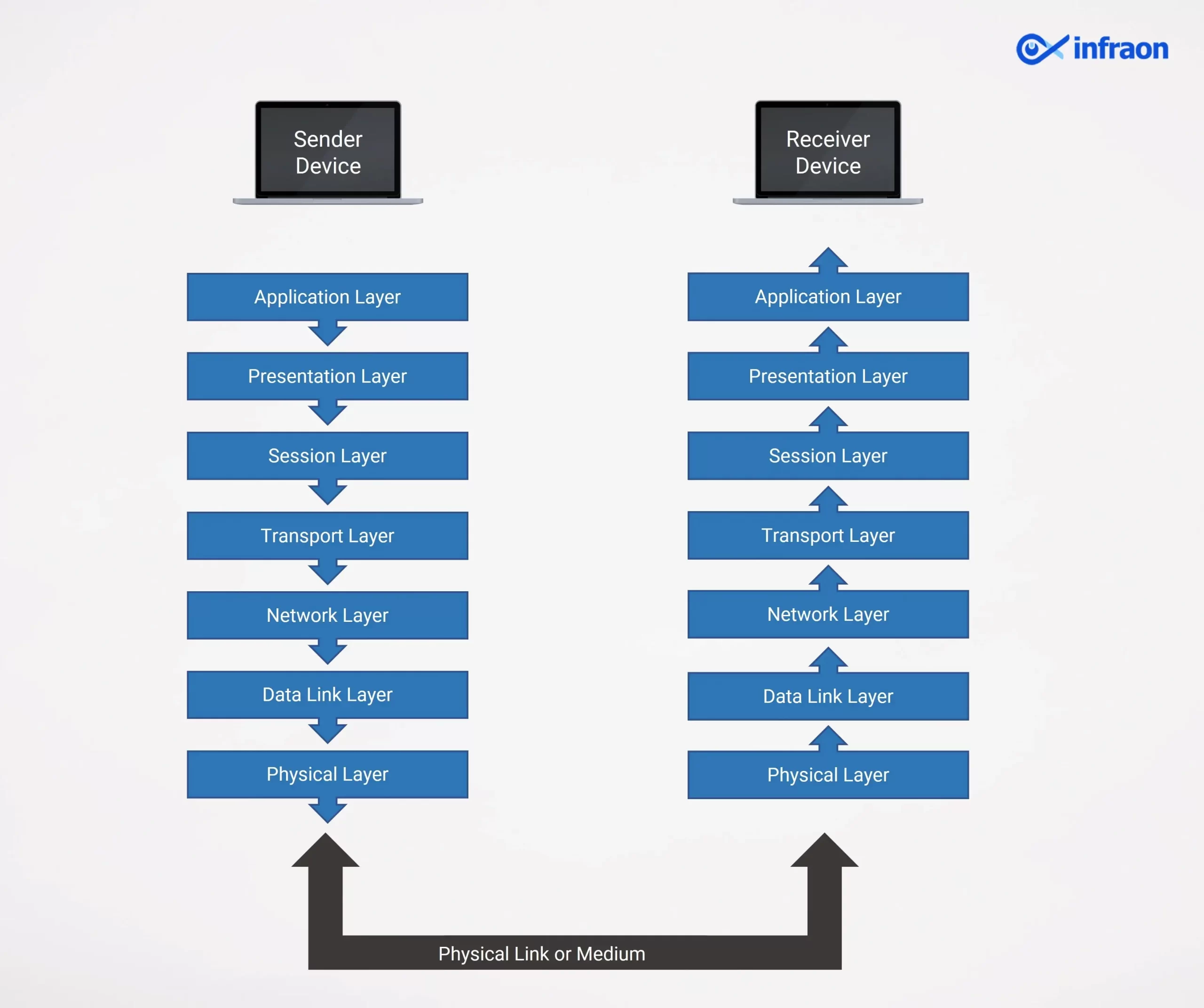
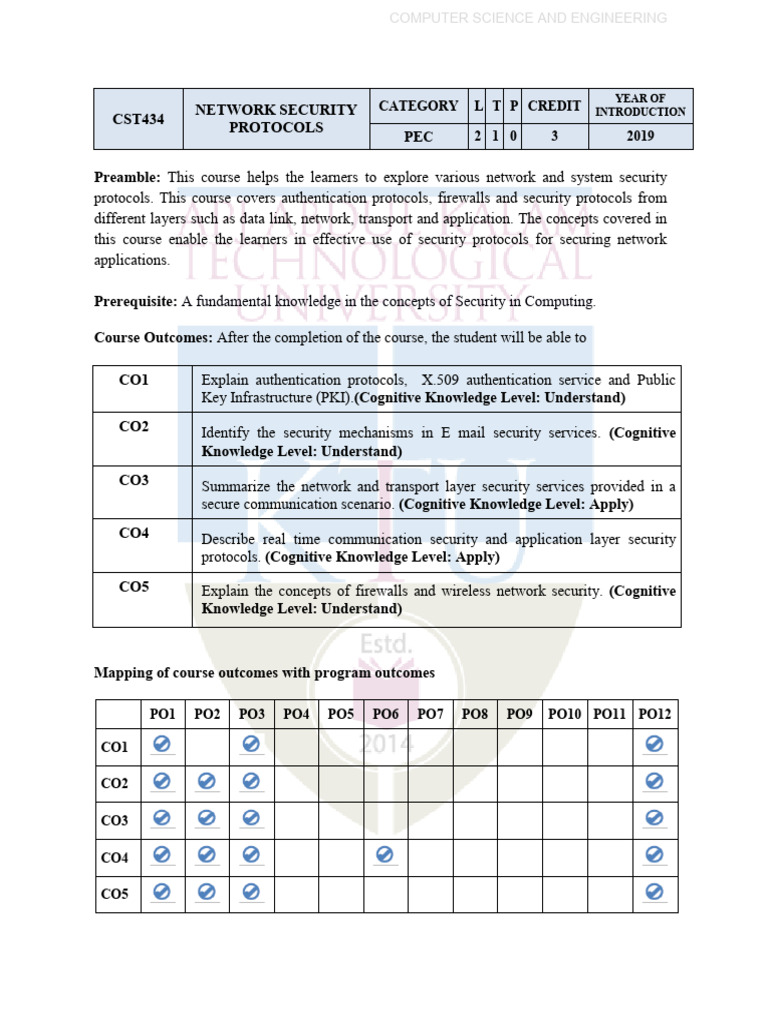
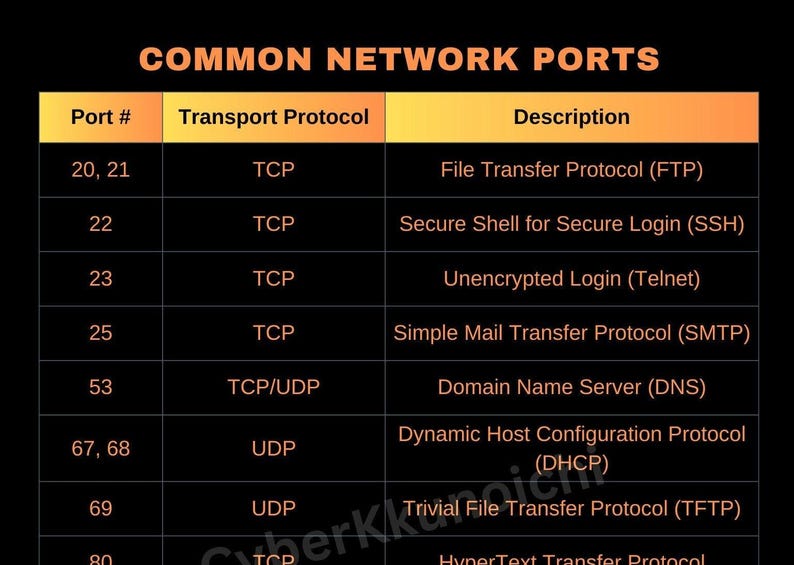
Network security protocols are sets of guidelines that protect the two aspects of the CIA triad - confidentiality and integrity of the data being transferred across a network. These protocols guard your data against cyber threats like unwanted access, manipulation, and destruction. Internet security protocols use encryption to keep data secure, ensuring that only authorized parties can access and read the data.
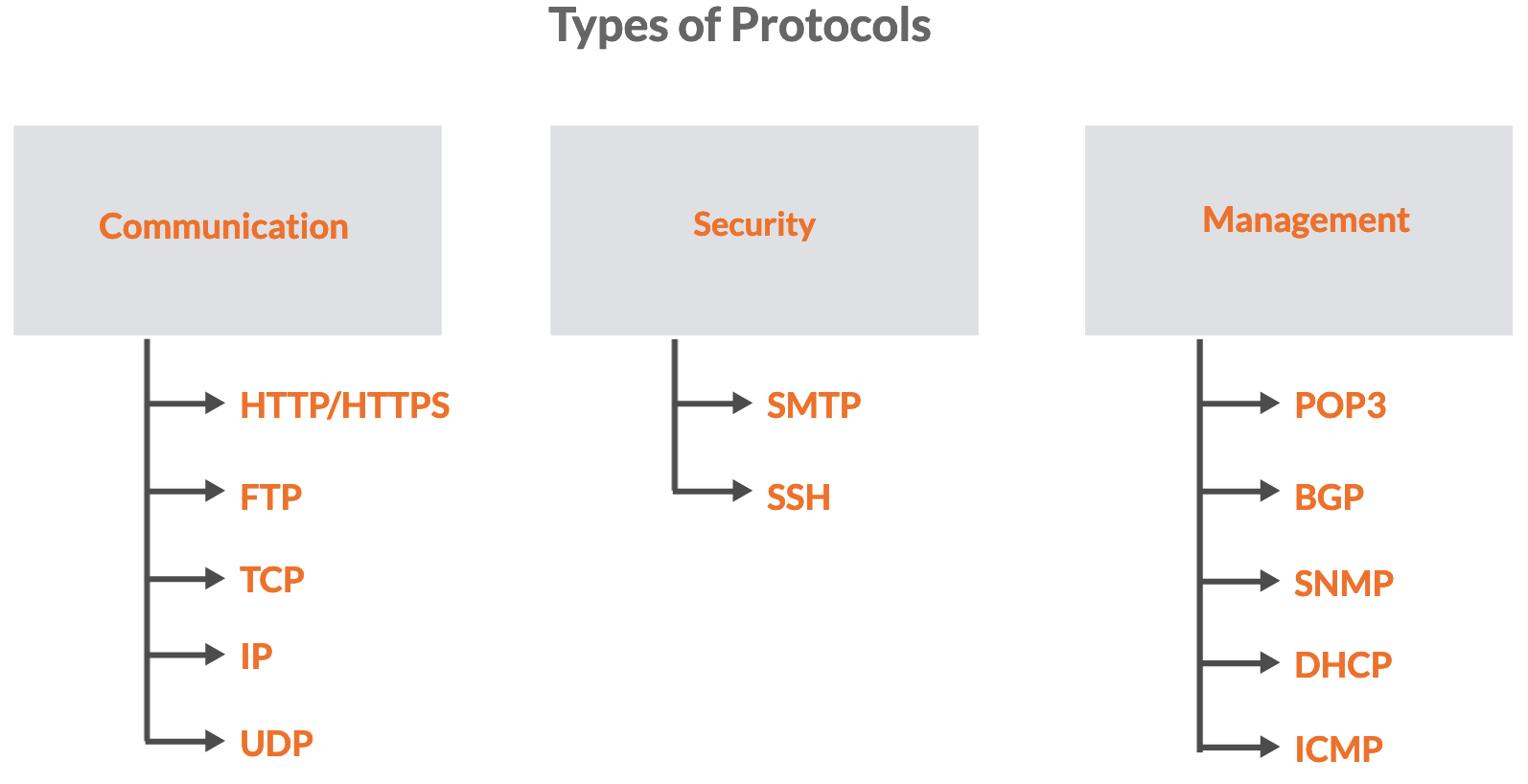
Types of G Network Security Protocols
There are several types of G Network Security Protocols available, each with its own strengths and weaknesses. Some of the most common types of G Network Security Protocols include:
- TLS (Transport Layer Security): TLS is an encryption protocol that provides secure communication between a web browser and a website. It ensures that data transmitted between the two parties remains confidential and secure.
- IPSec (Internet Protocol Security): IPSec is a suite of protocols that provides encryption and authentication for IP packets. It ensures the confidentiality, integrity, and authenticity of data transmitted across IP networks.
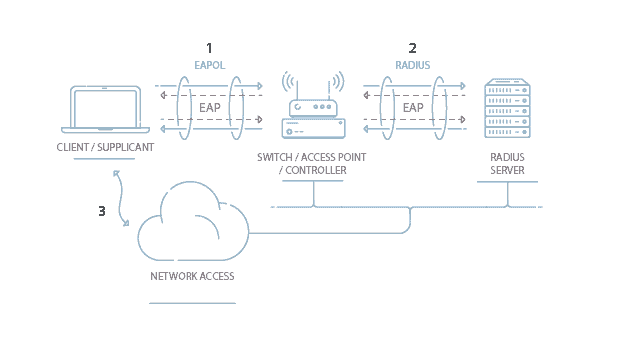
- SSH (Secure Shell): SSH is a secure protocol that allows users to access remote servers and devices securely. It uses encryption to keep data secure and prevent unauthorized access.
- SSL/TLS (Secure Sockets Layer/Transport Layer Security): SSL/TLS is a protocol that provides secure communication between a web browser and a website. It ensures that data transmitted between the two parties remains confidential and secure.
![Top 7 Network Security Protocols for Internet Safety [2025] Top 7 Network Security Protocols for Internet Safety [2025]](https://www.whatismyip.com/static/f13c11cfc592e0aa643a05e3680ab54f/network-protocols.webp)








![Network Security Protocols [An Easy-to-Read Guide] Network Security Protocols [An Easy-to-Read Guide]](https://www.collidu.com/media/catalog/product/img/d/1/d1d044535f85689516cfbc4fb8c96a2e31fad19069f1969f33225c2d795e9a84/network-security-slide6.png)