Setting Up a G Network for Security Information and Event Management
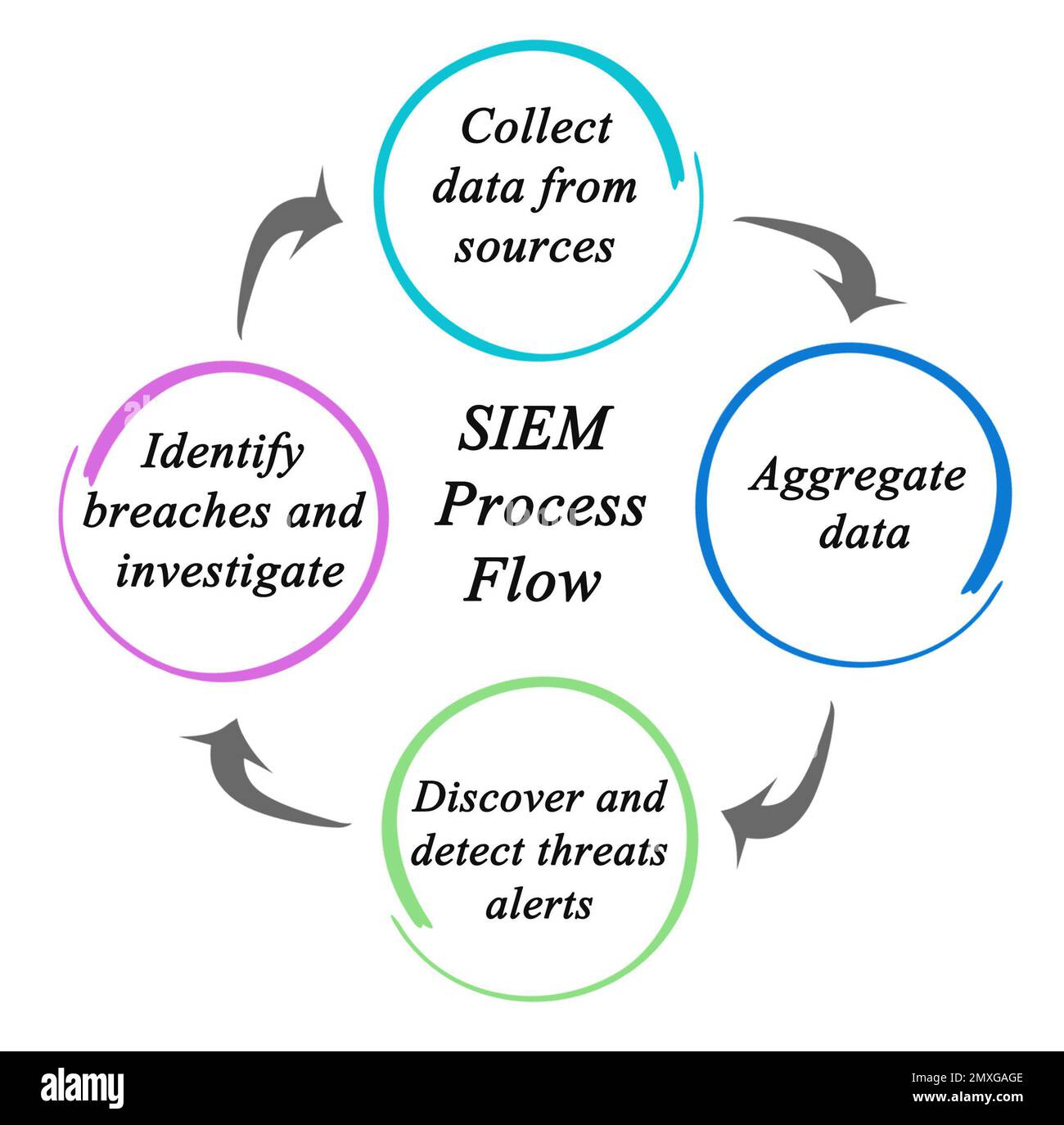
Aug 19, 2025, Security Information and Event Management (SIEM) deployment involves setting up and configuring a system to aggregate security event logs across an organization's infrastructure. This process requires careful planning, selection of the right SIEM solution, and configuration of data collection, correlation, and response mechanisms.
What is SIEM?
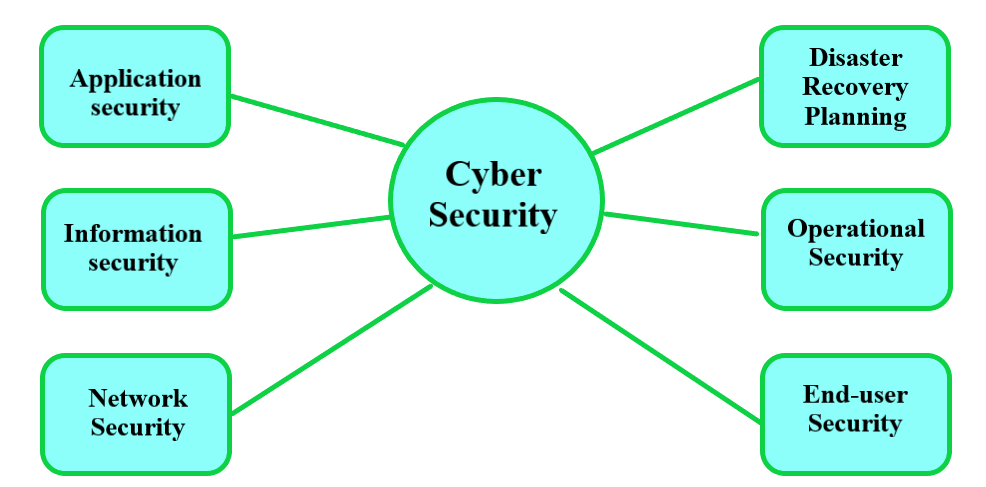
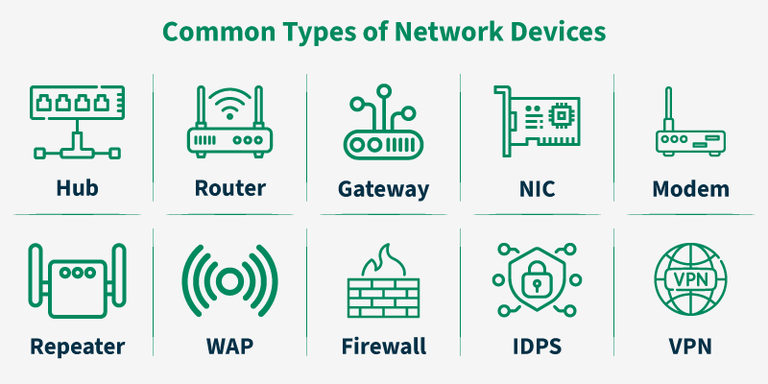
SIEM stands for Security Information and Event Management, and it is a tool designed to help organizations detect, respond to, and manage security threats in real-time by collecting and analyzing log data from across their entire IT environment. This includes servers, endpoints, applications, and network devices.
SIEM Key Features and Benefits
- Real-time visibility**: SIEM provides real-time visibility across an organization's security systems, enabling them to detect and respond to security threats in a timely manner.
- Event log management**: SIEM collects and aggregates log data from various sources, providing a centralized view of security-related events.
- Correlation and analysis**: SIEM uses predefined rules to correlate log and event data, identifying potential security incidents and generating alerts.
- Alerts and dashboards**: SIEM provides customizable alerts and dashboards that prioritize high-risk events, enabling security teams to focus on the most critical threats.
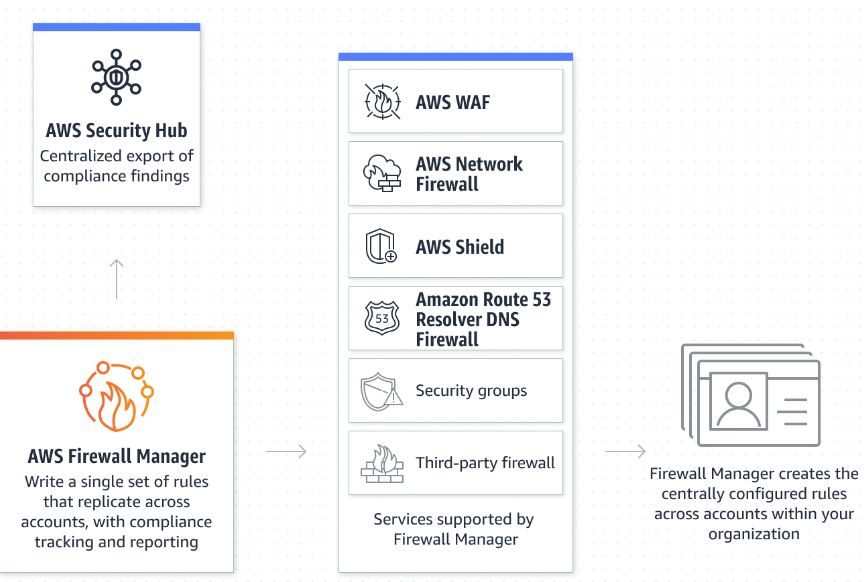
- Integration**: SIEM can integrate with existing security tools and technologies, providing a comprehensive view of security threats and incidents.