Setting Up a G Network for Zero Trust Security
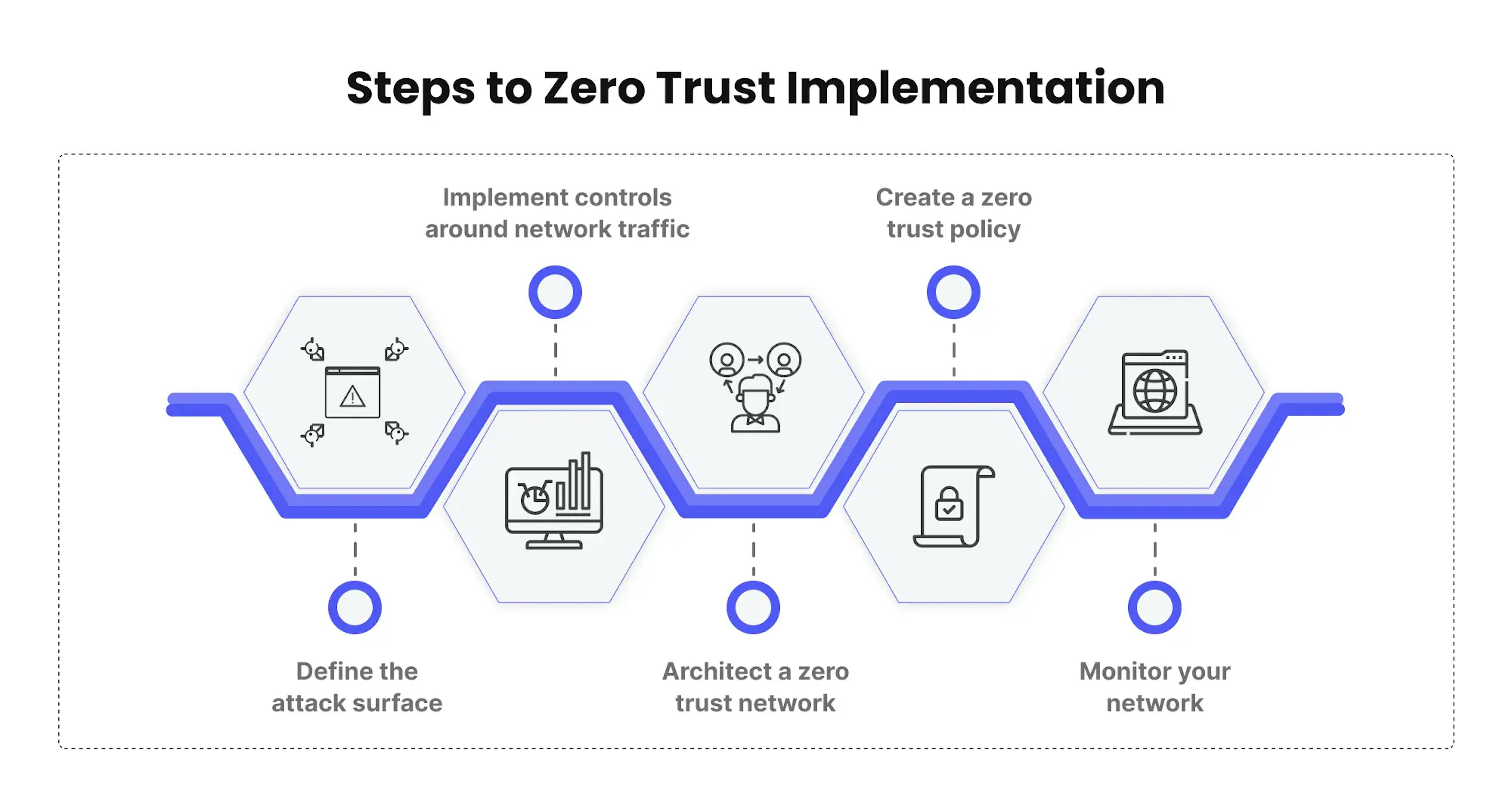
In today's digital age, cybersecurity is a top priority for businesses and organizations of all sizes. With the increasing number of cyber threats and data breaches, implementing a zero-trust security model has become a necessity. In this article, we will explore the concept of zero-trust security, its benefits, and provide a step-by-step guide on setting up a zero-trust network for enhanced security.
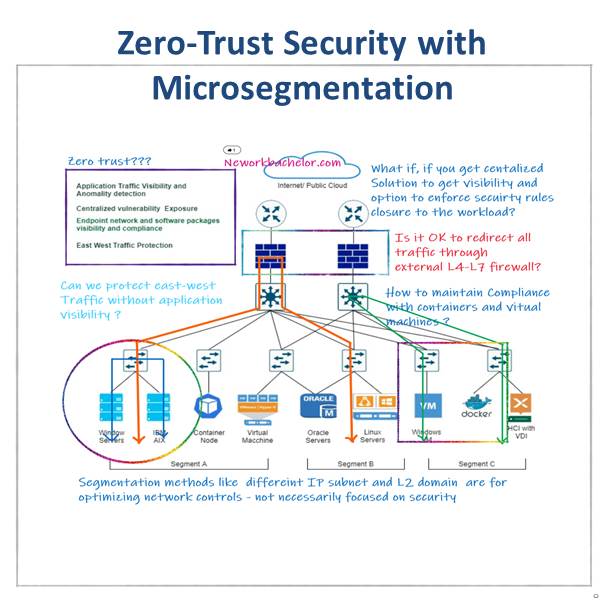
What is Zero-Trust Security?
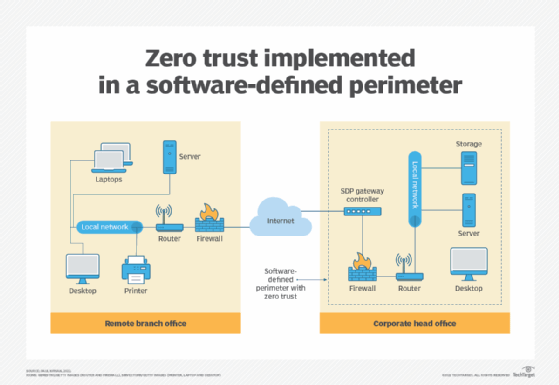
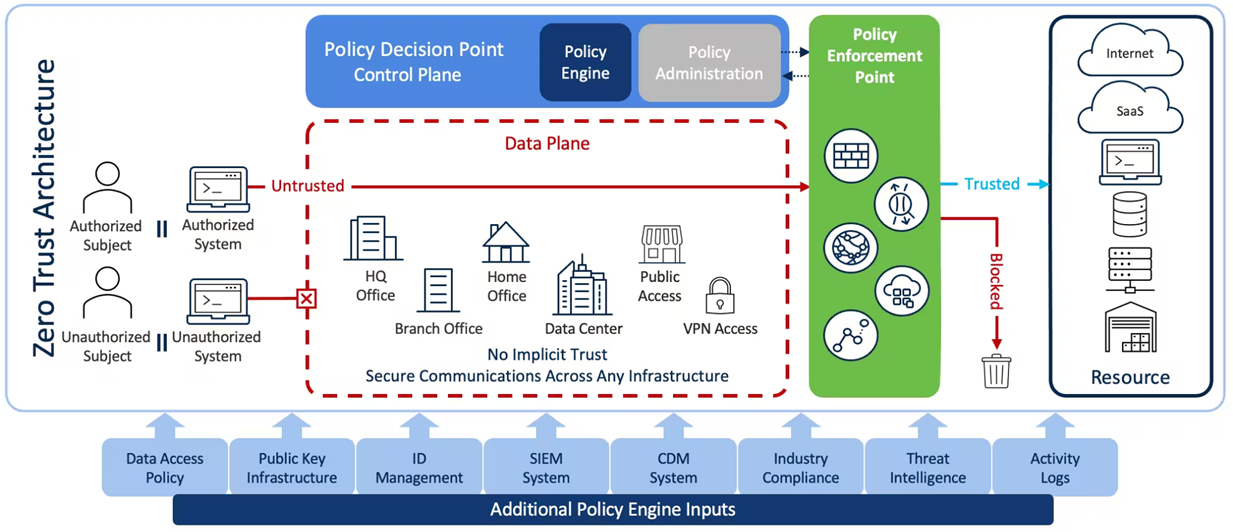
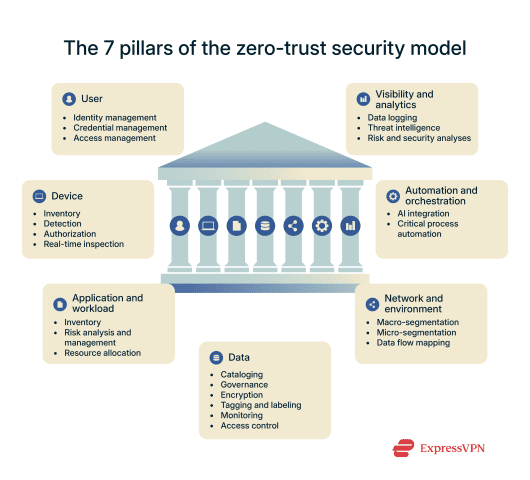
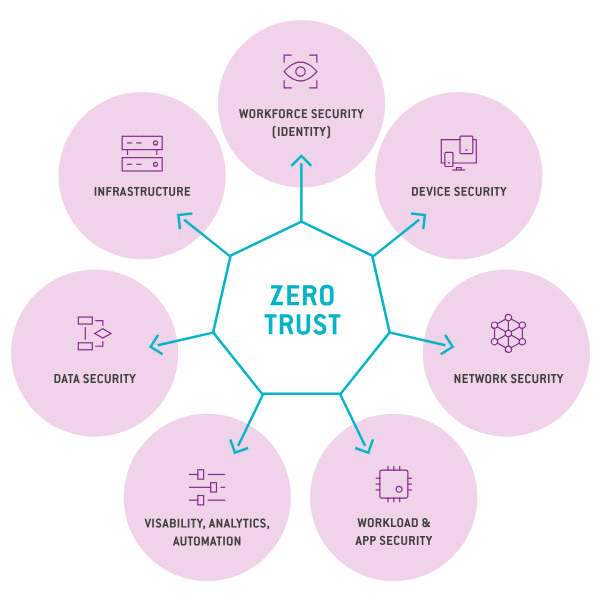
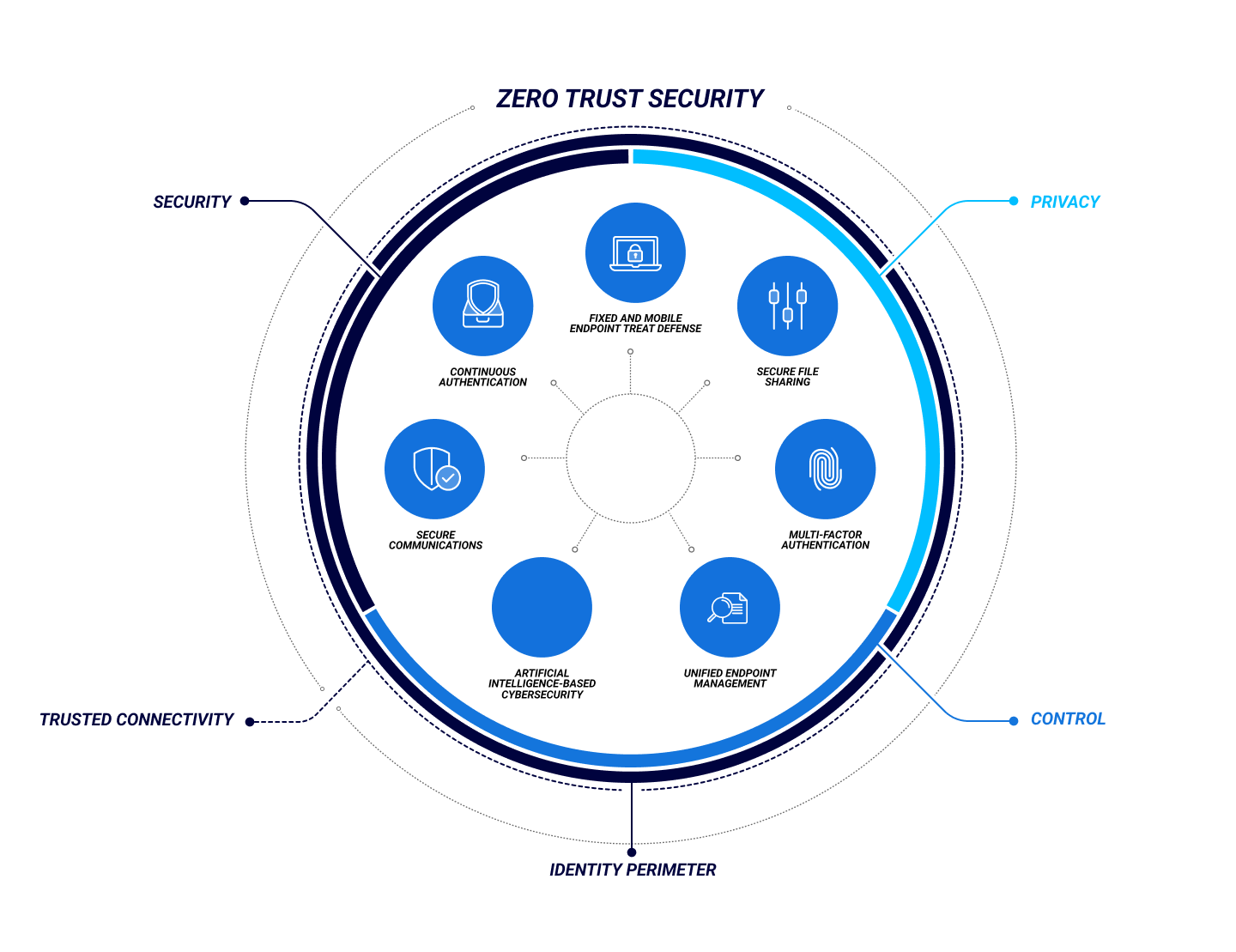
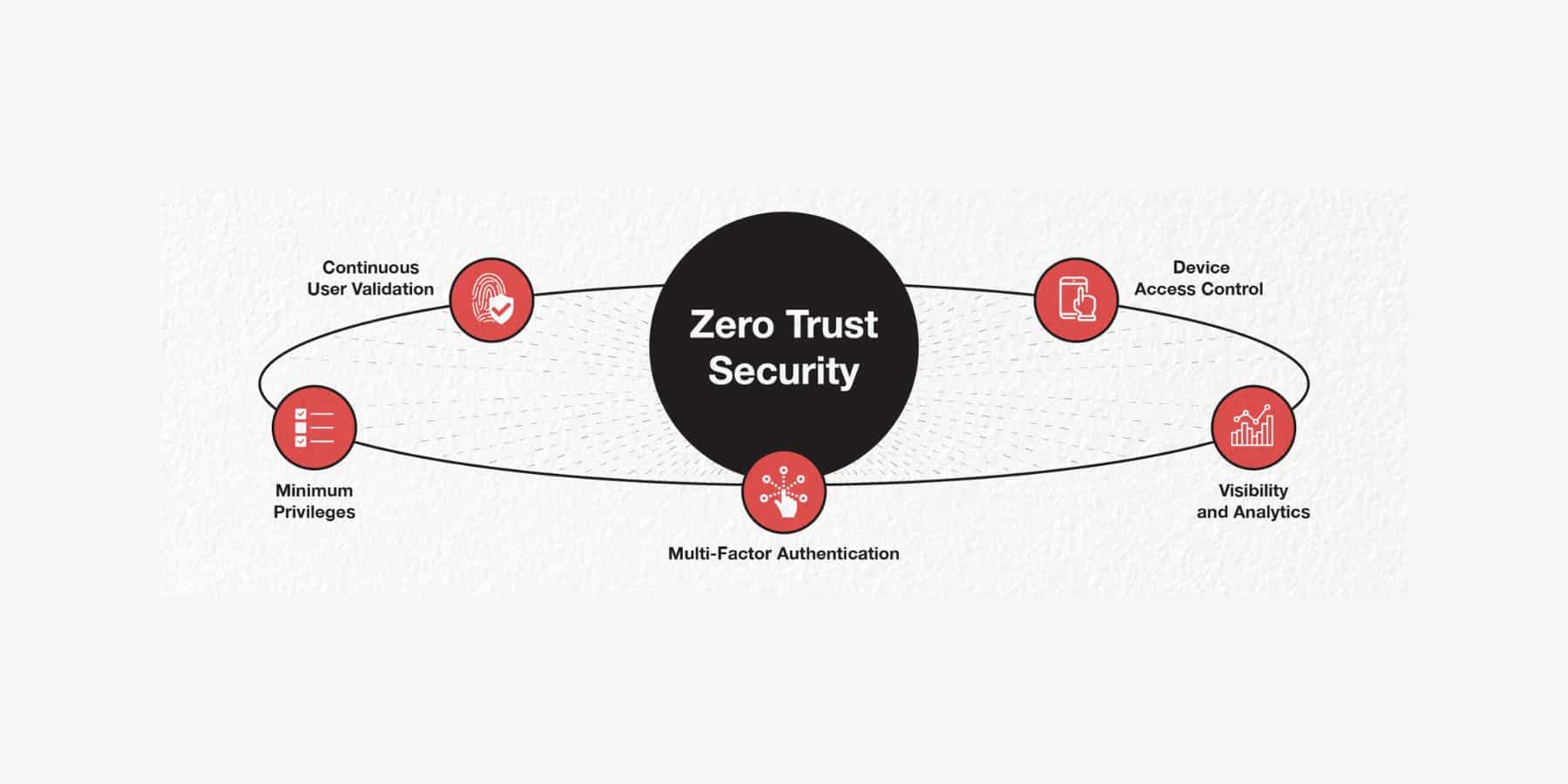
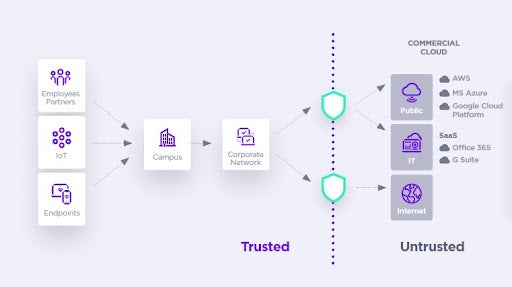
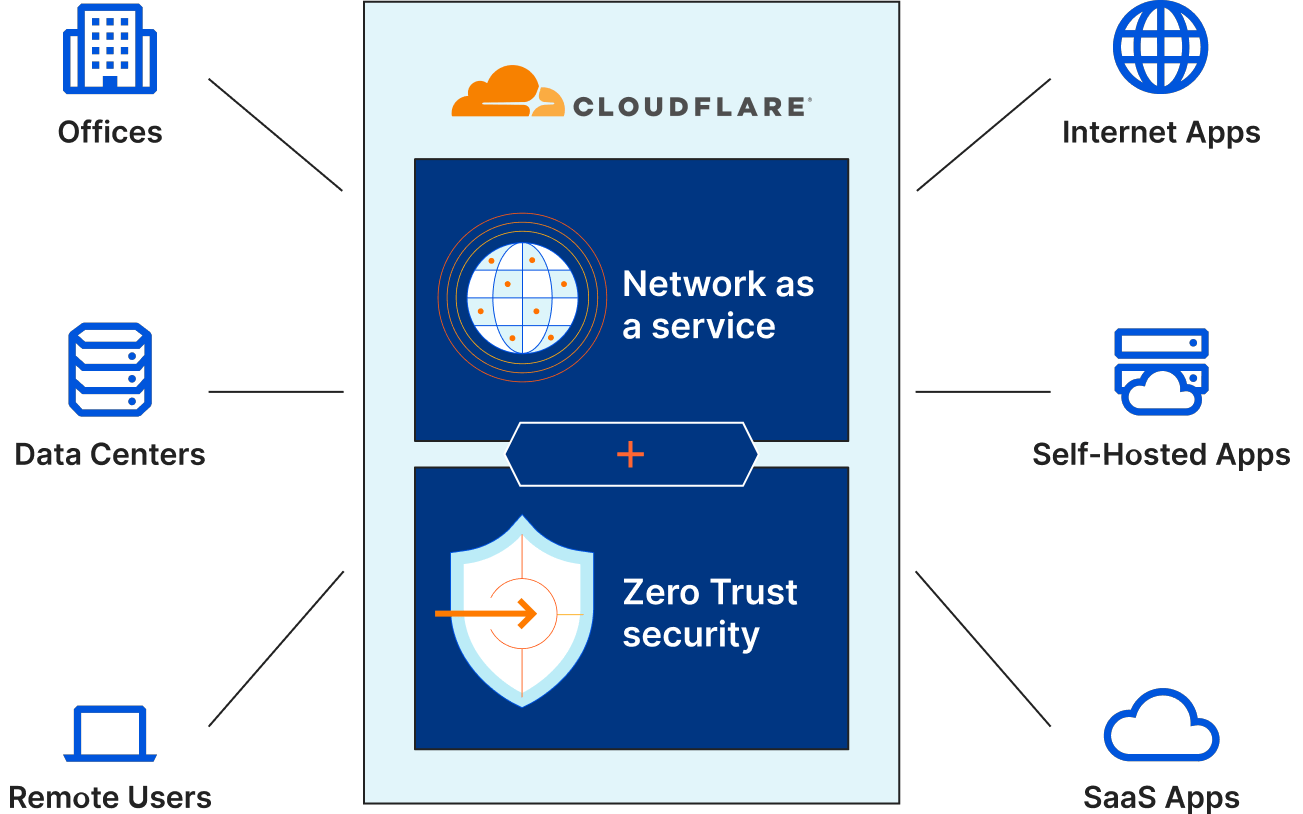
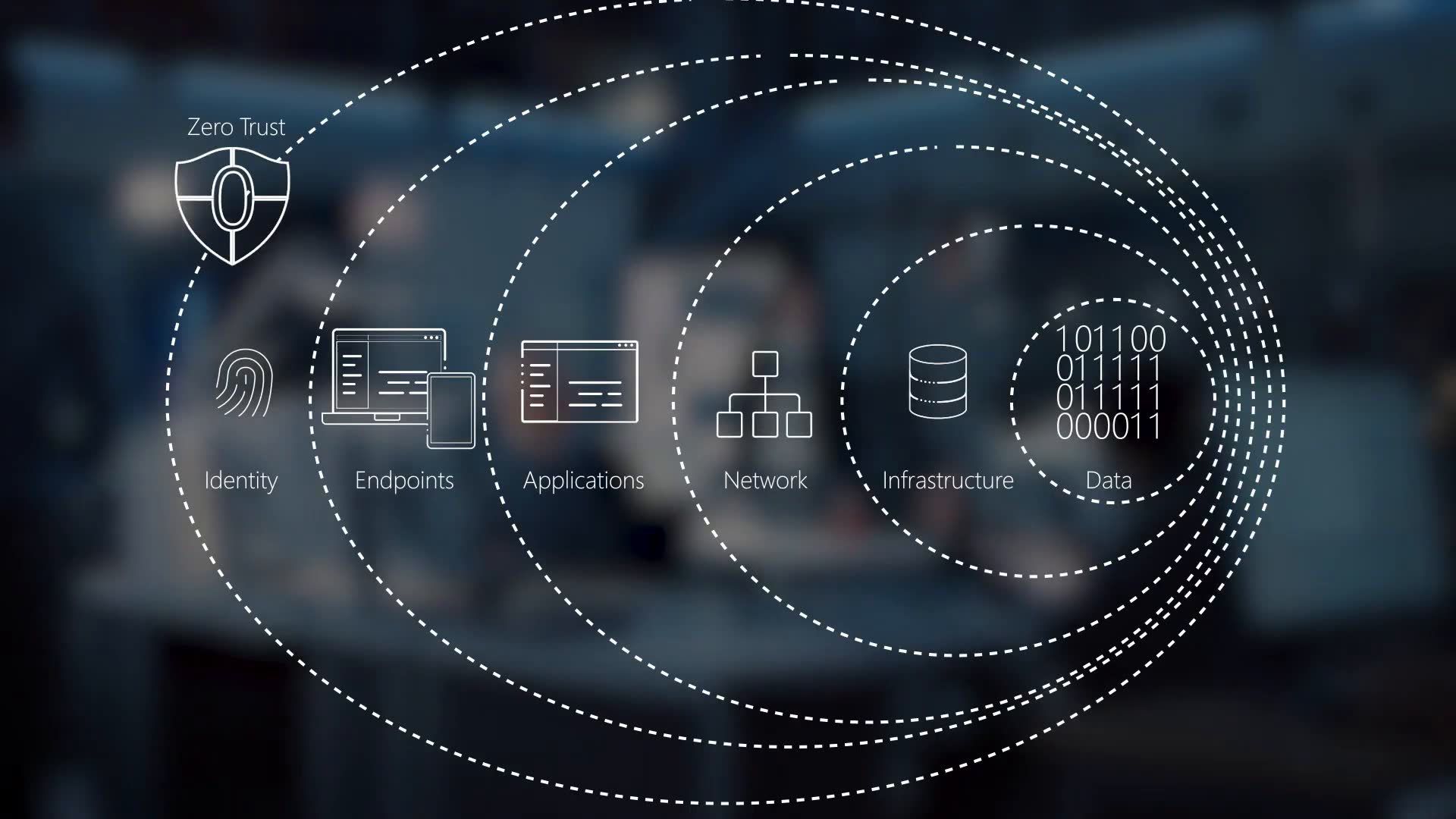
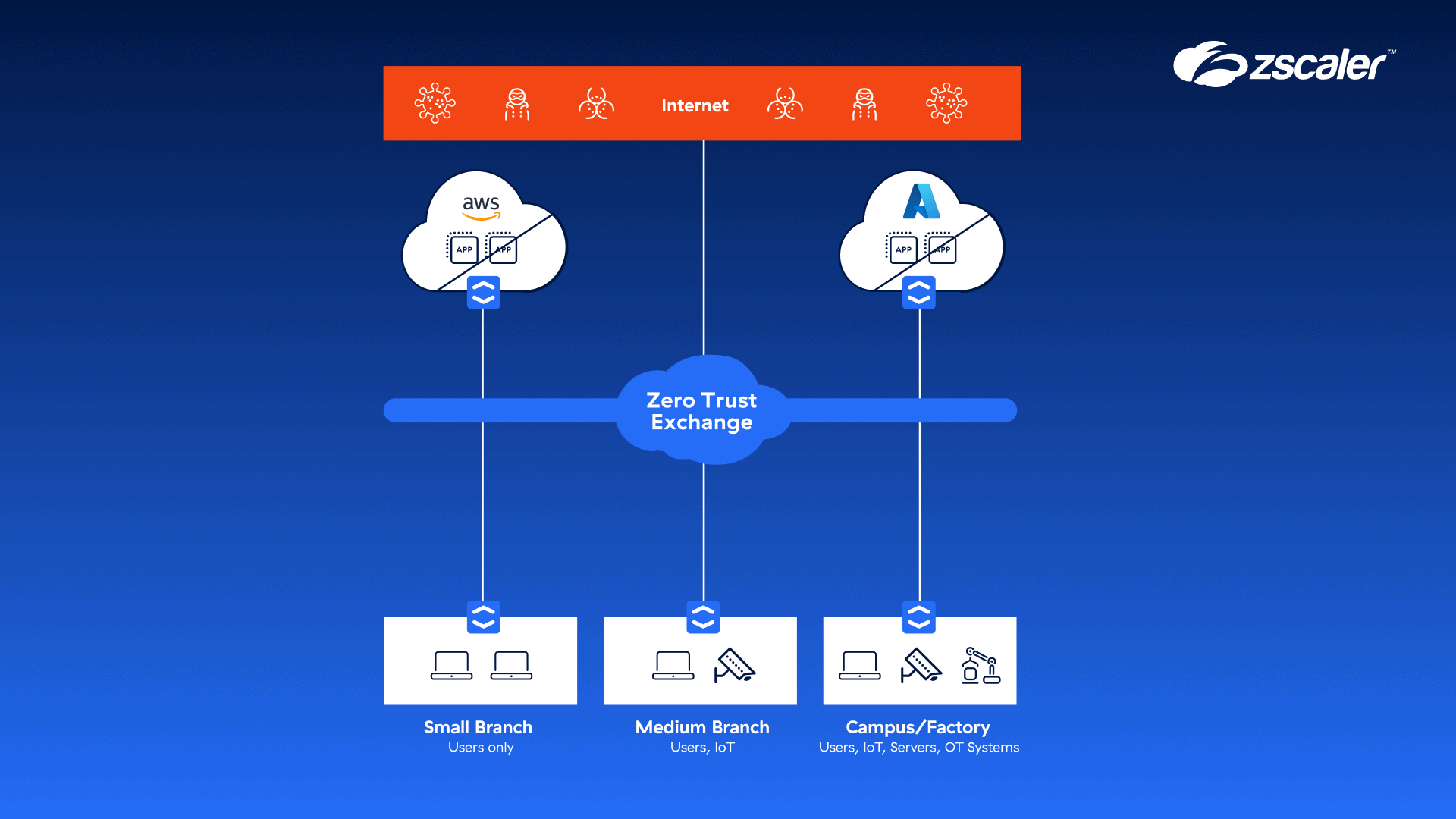
Zero-trust security is a cybersecurity approach that assumes all users and devices are potentially malicious. It focuses on protecting resources, not just network segments, and verifies the identity and authorization of every user and device before granting access to sensitive information and systems. This approach eliminates the concept of a trusted network or perimeter, making it a robust defense against cyber threats.
Benefits of Zero-Trust Security
- Enhanced security: Zero-trust security reduces the attack surface by verifying every user and device before granting access.
- Improved compliance: Zero-trust security helps organizations meet regulatory requirements by verifying identity and authorization.
- Better incident response: Zero-trust security enables organizations to detect and respond to security incidents more effectively.
- Reduced risk: Zero-trust security reduces the risk of data breaches and cyber attacks.